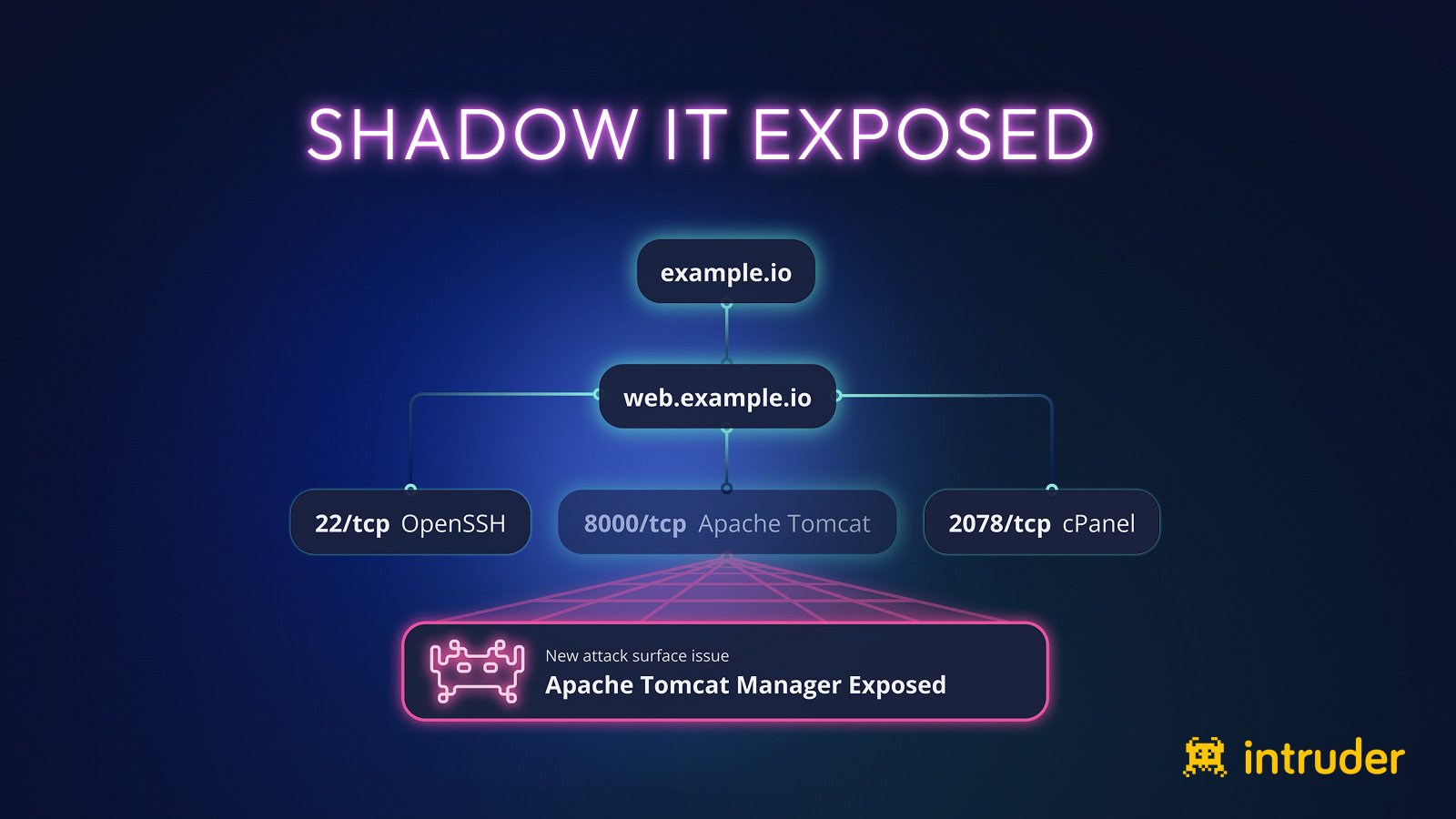
Shadow IT Is Expanding Your Attack Surface. Here’s Proof
Shadow IT isn’t theoretical—it’s everywhere. Intruder uncovered exposed backups, open Git repos, and admin panels in just days, all hiding sensitive data. Make your hidden assets visible before attackers do. […]BleepingComputerRead More