Tokens per watt (TpW) – the measure of useful AI work produced per watt of energy consumed – is the
Life with the Penguin
Recent news
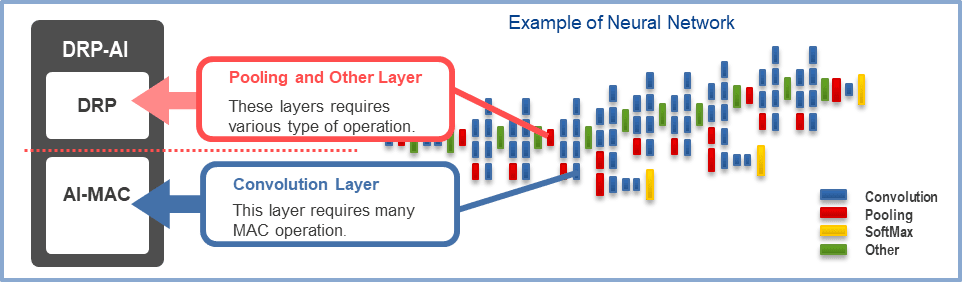
A look into Ubuntu Core 26: Deploying AI models on Renesas RZ/V series for production
Welcome to this blog series which explores innovative uses of Ubuntu Core. Throughout this series, Canonical’s Engineers will show what

RISC-V profiles – why is RVA23 significant?
Introduction One of the important offerings of the RISC-V Instruction Set Architecture (ISA) is the ability to customize and extend

AI with AMD ROCm on Ubuntu: your questions answered
AMD ROCm is now available in Ubuntu 26.05 LTS. Learn what how to make the best of it, and find
Latest

Agentic AI hype races ahead as enterprises remain stuck in pilot mode
Most orgs remain trapped between flashy demos and real-world deployment, despite 75% saying adoption is racing aheadwww.theregister.com – ArticlesRead More

Ubuntu and Ubuntu Pro on Azure Cobalt 200 VMs
Microsoft has announced the preview of Azure Cobalt 200, its second-generation custom Arm silicon. Learn how Ubuntu and Ubuntu Pro
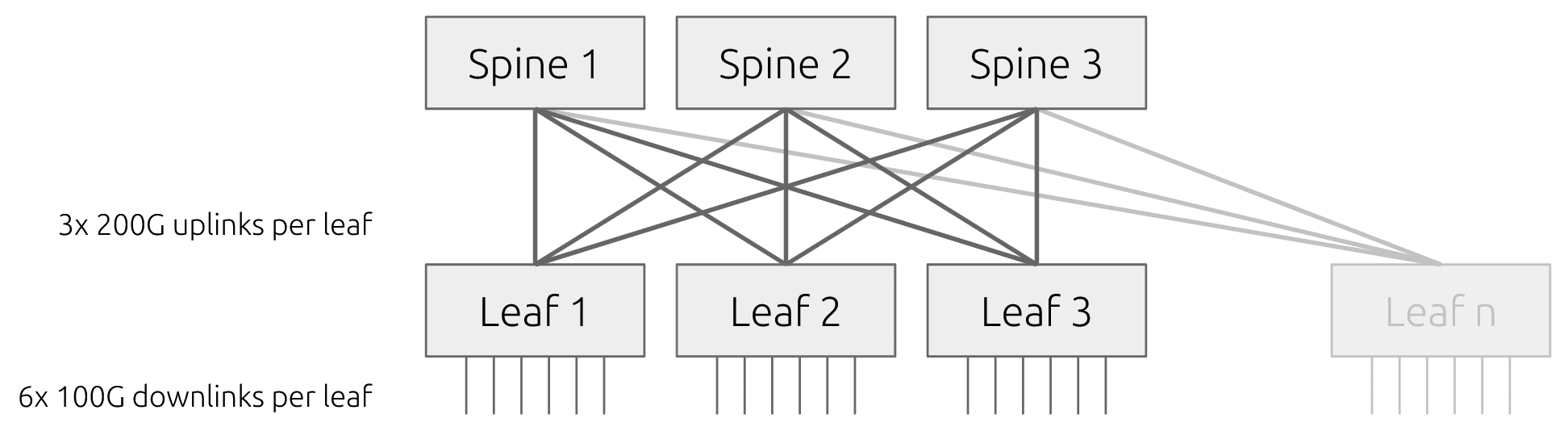
What is InfiniBand?
When distributed workloads stall because nodes cannot exchange small messages quickly and consistently, the network is the limiting factor. How
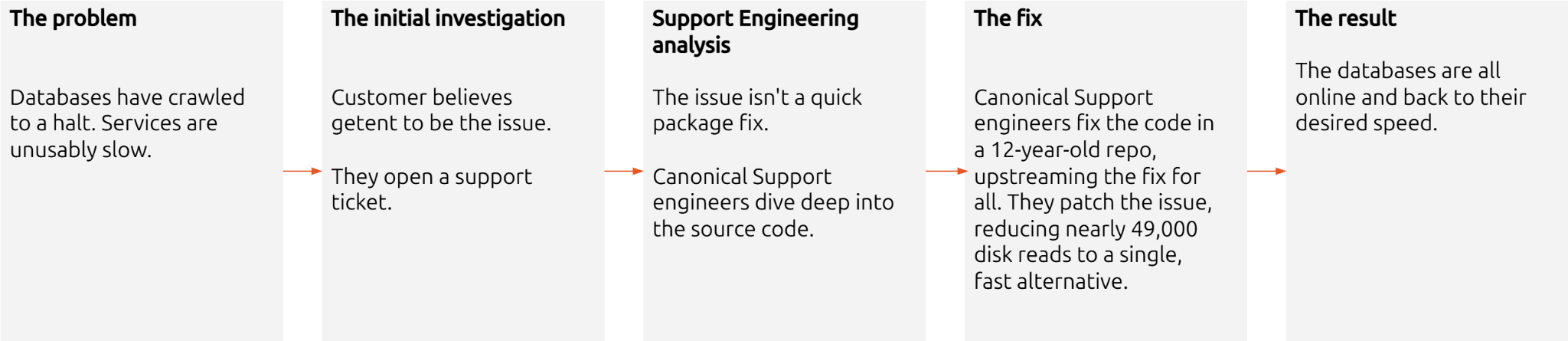
How Canonical Support solves hard Linux performance bugs – even in 12-year old code
A 12-year-old bug in libnss-db caused getent enumeration to slow to a crawl – and showed how far expert support

Securing AI agent workflows on Ubuntu with the new NVIDIA OpenShell snap
By packaging OpenShell as a snap, Canonical is enabling enterprises to confidently run next-generation agentic workflows across local devices, hybrid

PinTheft Linux kernel vulnerability mitigation
A local privilege escalation (LPE) security vulnerability in the Linux kernel, codename “PinTheft,” was publicly disclosed on May 19, 2026.

Canonical announces optimized Ubuntu images for TPU virtual machines by Google Cloud
Canonical and Google Cloud announced the availability of certified Ubuntu images for Google’s Cloud TPU Virtual Machines.Ubuntu blogRead More
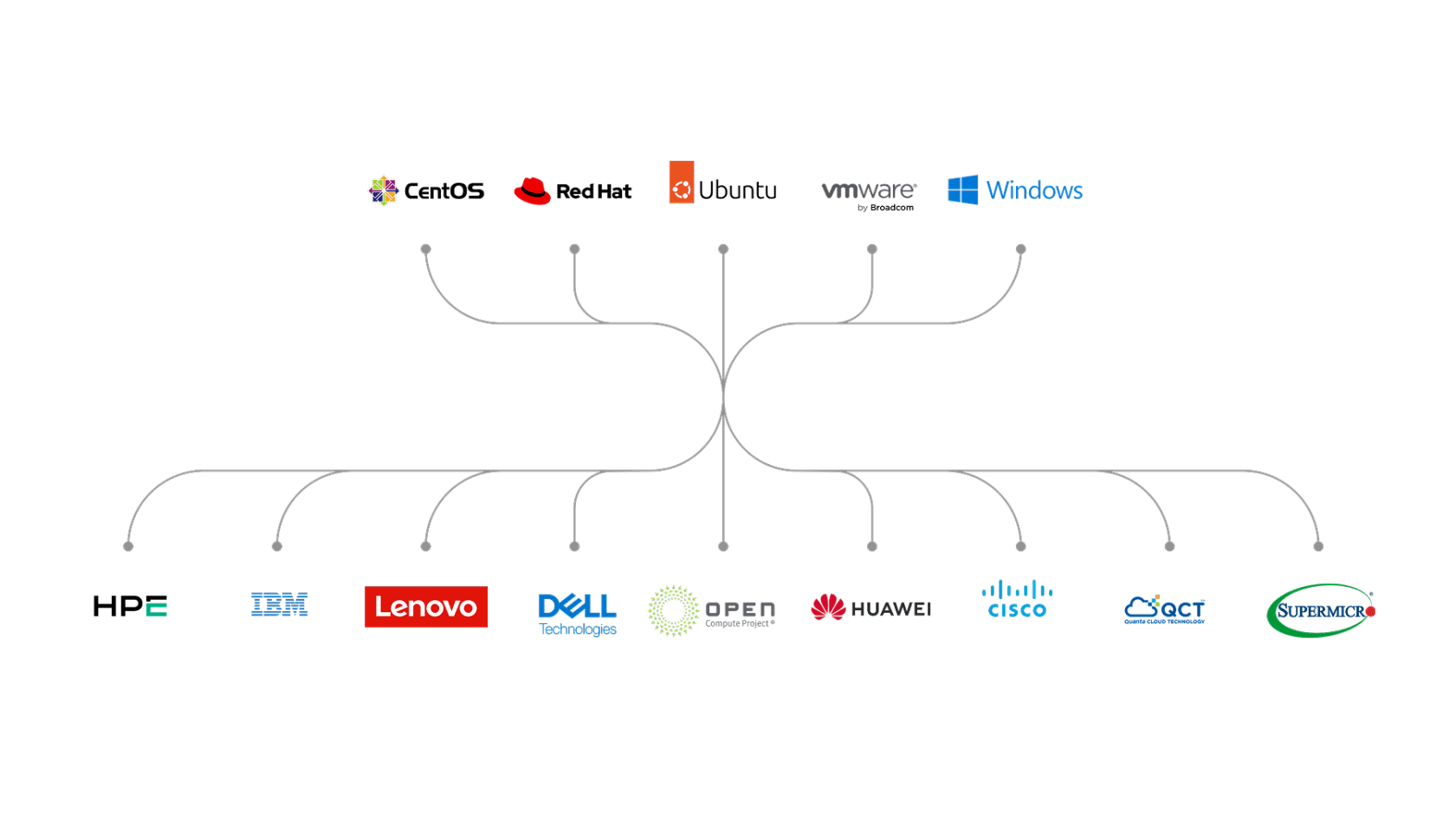
VMware hypervisor deployment using MAAS
Most modern datacenters are inherently heterogeneous. VMware environments coexist with container platforms, databases, and other bare-metal workloads, often on the

Introducing Workshop: launch sandboxed development environments on Ubuntu with a single command
Developers now benefit from consistency and repeatability for cutting-edge workflows, including agentic AI. Today, Canonical announced the release of Workshop,

Decoding design: How design and engineering thrive together in open source
Open source thrives on engineering-driven processes. Fast feedback loops, terminal tools, Git workflows: they’re the lifeblood of how we build

Migrating from Apache Spark 3 to Spark 4
The purpose of this guide is to highlight the key differences between Apache Spark 3 and Spark 4, and provide
PAM: Important Risks in Linux Authentication Trust Chain
PAM sits at the center of Linux authentication. Every login, SSH session, and privilege escalation request runs through it. It
Critical Linux-PAM Vulnerability Exposes Servers to Local Privilege Escalation
A newly disclosed vulnerability in Linux’s Pluggable Authentication Module (PAM) system is making waves in the security community. Known as

TARmageddon: async-tar Vulnerability Exposes Linux Archive Extraction Risks
A path traversal flaw in the Rust async-tar library has people looking harder at archive extraction security on Linux. Researchers

The Linux Command Line: Bridging Security Awareness for Sysadmins
I’ve been around Linux long enough to stop expecting much from intro books. Most of them walk through commands ”

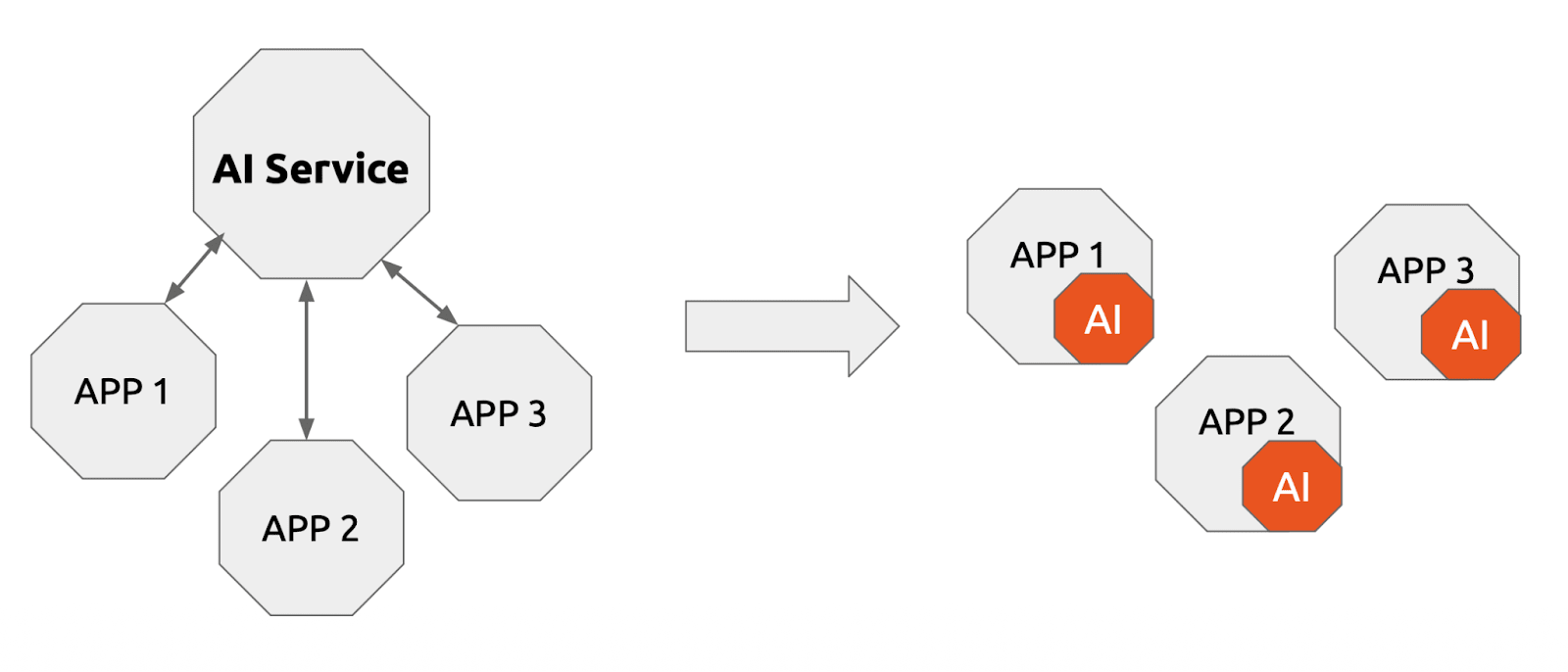
Run agentic workloads on Arm and Ubuntu
The era of prompt-and-response AI is behind us. We are now firmly in the age of agentic AI and the
Developing web apps with local LLM inference
I’ve yet to meet a developer that enjoys working with metered AI APIs. The need to pay for every API

Canonical announces fully Managed Kubeflow AI operations platform on the Microsoft Azure Marketplace
Canonical has announced the general availability of Managed Kubeflow on the Microsoft Azure Marketplace. This fully managed MLOps platform allows

A look into Ubuntu Core 26: Cloud-powered edge computing with AWS IoT Greengrass and Azure IoT Edge
Welcome to this blog series which explores innovative uses of Ubuntu Core. Throughout this series, Canonical’s Engineers will show what

CVE-2026-46333 (ssh-keysign-pwn) Linux kernel vulnerability mitigations
An information disclosure security vulnerability in the Linux kernel was publicly disclosed on May 15th, 2026. The vulnerability was reported
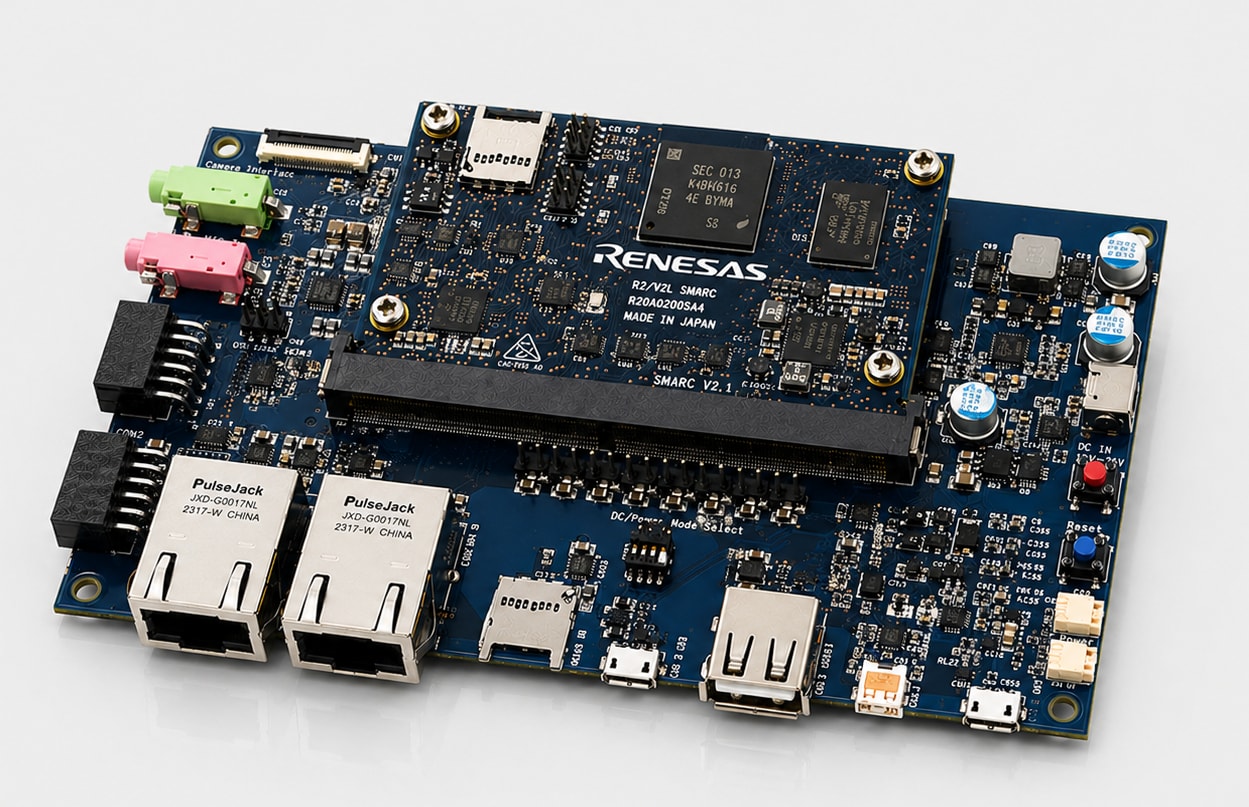
Canonical launches Ubuntu Core 26
Ubuntu Core 26 introduces precise Linux builds, optimized OTA updates, live kernel patching, and enhanced hardware-backed protection for mission-critical deployments.



