Microsoft Threat Intelligence identified a prompt injection pathway in Claude Code GitHub Action that allowed access to workflow secrets under
Vendors' News
Vendor announcements

YARA Rules: A Complete Guide with Best Practices and Use Cases
YARA rules are one of the most practical ways to turn malware analysis into repeatable detection. They help analysts describe

Elon Musk’s XChat: how secure is the new messaging app? | Kaspersky official blog
Breaking down Elon Musk’s XChat: how its end-to-end encryption works, why experts have slammed its PIN system, and how the

Your AI bill is out of control. Cloudflare can fix it now.
AI Gateway now features real-time spend limits to prevent runaway token bills across multiple AI providers. By integrating with Cloudflare

Threat Brief: Active Exploitation of PAN-OS CVE-2026-0257
We include indicators of activity and mitigations for PAN-OS vulnerability CVE-2026-0257. The post Threat Brief: Active Exploitation of PAN-OS CVE-2026-0257

The Good, the Bad and the Ugly in Cybersecurity – Week 23
US Treasury sanctions Iran’s largest crypto exchange, PRC-linked TA4922 expands phishing to Europe and Africa, attackers exploit Palo Alto VPN

Cisco Live U.S.: Leading in the agentic AI age
With key announcements around Cisco Cloud Control, Cisco IQ, Live Protect, and more, Cisco solidifies its critical role in driving
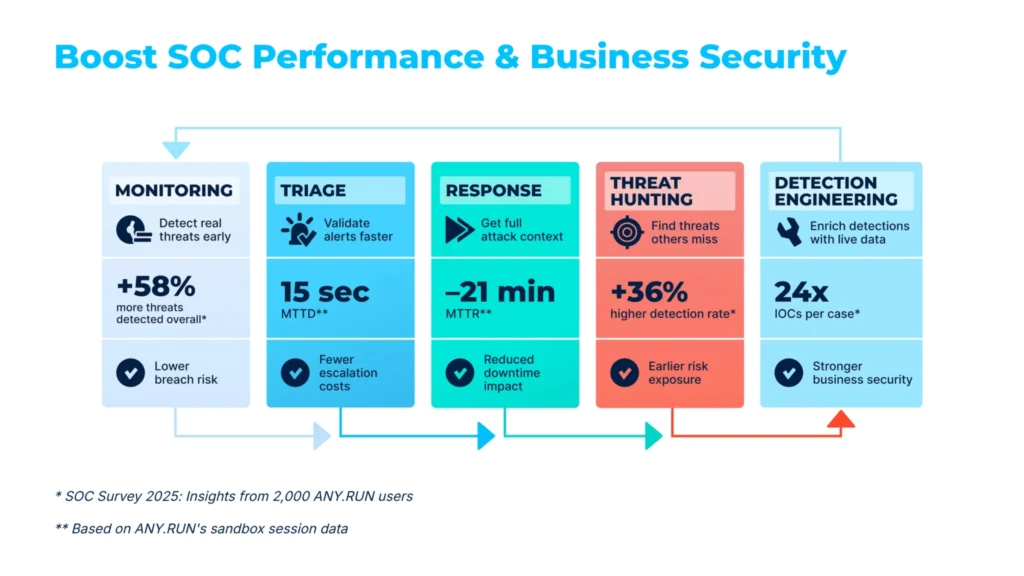
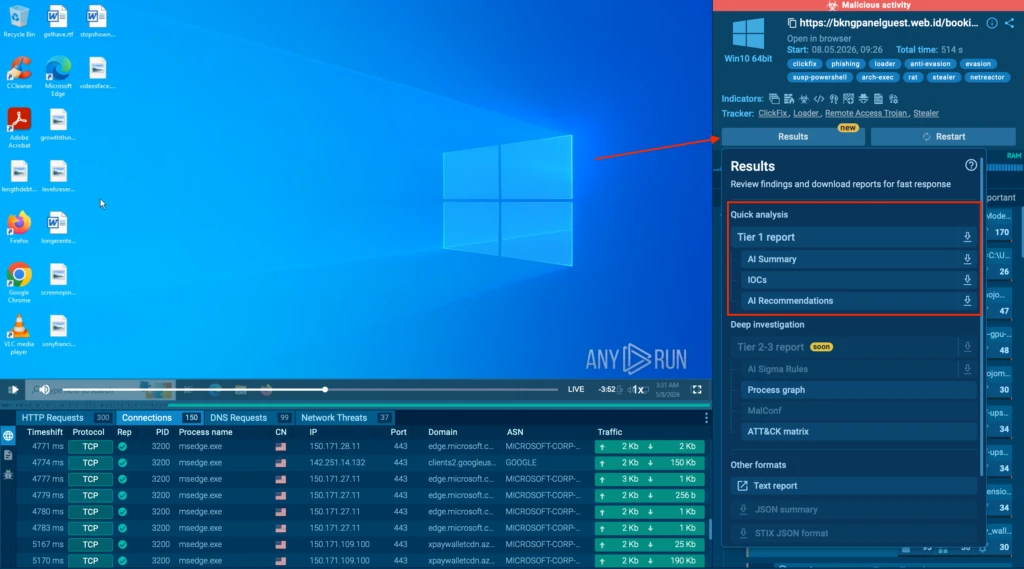
Leader in Malware Analysis: ANY.RUN Named Top Vendor in G2 Summer 2026 Awards
We are proud to announce that ANY.RUN has earned the title of Momentum Leader and ranked #1 in the Relationship Index in the latest G2 Summer

The RIPE Chair Team Reports – Highlights from RIPE 92
From governance and policy to AI and research, RIPE 92 sparked lively discussion across the community. The RIPE Chair Team

PolarProxy 2.0.1 Released
Our TLS inspection proxy PolarProxy has been updated with bug fixes, improved performance and more reliable PCAP output. The recent
Quarterly WordPress Threat Intelligence Report – Q1 2026
As the industry leader in WordPress security we have access to attack telemetry and vulnerability intelligence that no other security

Updating the taxonomy of failure modes in agentic AI systems: What a year of red teaming taught us
A surge in real-world attacks against agentic AI systems is reshaping how we think about risk. Based on 12 months
The Detection & Response Chronicles: Covert Operations Through QEMU
Adversaries have always relied on legitimate tools to carry out their attacks. These tools are already trusted by security solutions,
Wordfence Intelligence Weekly WordPress Vulnerability Report (May 25, 2026 to May 31, 2026)
Last week, there were disclosed in and that have been added to the Wordfence Intelligence Vulnerability Database, and there were

VoidZero is joining Cloudflare
VoidZero, the team behind Vite, Vitest, Rolldown, Oxc, and Vite+, is joining Cloudflare. Vite stays open source, vendor-agnostic, and built
Latest

Agentic AI hype races ahead as enterprises remain stuck in pilot mode
Most orgs remain trapped between flashy demos and real-world deployment, despite 75% saying adoption is racing aheadwww.theregister.com – ArticlesRead More

Agentic AI hype races ahead as enterprises remain stuck in pilot mode
Most orgs remain trapped between flashy demos and real-world deployment, despite 75% saying adoption is racing aheadwww.theregister.com – ArticlesRead More

China Mobile Jiangsu and ZTE unveil intelligent complaint analysis agent to reshape core network O&M
PARTNER CONTENT: Leveraging multi-modal LLMs and agent technology to automate signaling analysis and shift core network O&M from experience to

ZTE showcases AI-driven project management innovations at the 14th IPMA Research Conference 2026
PARTNER CONTENT: Integrating AI into the iEPMS platform to achieve a 98% quality review accuracy rate and slash report generation

Trump pumps federal funds into coal plants in the name of energy security
DoE wants to keep 13 coal-fired power generators going at the same time as funding nuclear researchwww.theregister.com – ArticlesRead More

Serious ISS air leak forces NASA astronauts to temporarily take shelter in Dragon capsule
Business is back to normal in the orbital station, but one of two newly discovered leaks is still unrepairedwww.theregister.com –

Peering Capacity at Public Internet Exchanges: What the Data Reveals
This study delivers data-rich insights into the decisions made by the most IXP-connected CDN, cloud and content networks, analysing their

Q1 2026 Cyber Risk Report: Insights from 2.1 Million Malware and Phishing Investigations
Based on 2,101,483 malware and phishing investigations from Q1 2026, ANY.RUN‘s Cyber Risk report provides a real-world view of modern attack trends. It covers trending malware families, TTPs, and other technical

Enforcing the First AS in BGP AS_PATHs
BGP is vulnerable to routing hijacks and path leaks that negatively impact traffic on the Internet. RPKI helps solve some

Study on the Wi-Fi security situation in Mexico | Kaspersky official blog
Kaspersky experts have investigated the security of public Wi-Fi access points in Mexico City, Guadalajara, and Monterrey.Kaspersky official blogRead More

KASG: security gateway for autonomous vehicles | Kaspersky official blog
How Kaspersky Automotive Secure Gateway (KASG) ensures vehicle security and why SIEM integration is essential.Kaspersky official blogRead More
Attackers Actively Exploiting Critical Vulnerability in Everest Forms Pro Plugin
On March 30th, 2026, we publicly disclosed a critical Remote Code Execution vulnerability in Everest Forms Pro, a WordPress plugin

Impersonation, Click Hijacking, and TDS: Inside a Malware Distribution Ecosystem
Research by: Alexey Bukhteyev Key Takeaways Introduction When we search Google for a popular piece of software, we usually click the
Release Notes: Decision-Ready SOC Reporting, Elastic Security Integration, and 1400+ Threat Coverage Updates
Security leaders are under growing pressure to reduce the time between threat detection and response without adding more complexity to

TA4922: The Suspected Chinese Crime Group is Going Global
Key Findings: TA4922 is a highly sophisticated threat actor demonstrating a rapid operational tempo and continually evolving malware arsenal. The group has
Argamal: Malware hidden in hentai games
Kaspersky researchers analyze new Argamal RAT distributed via infected hentai games and allowing the attacker to control the target machine.SecurelistRead
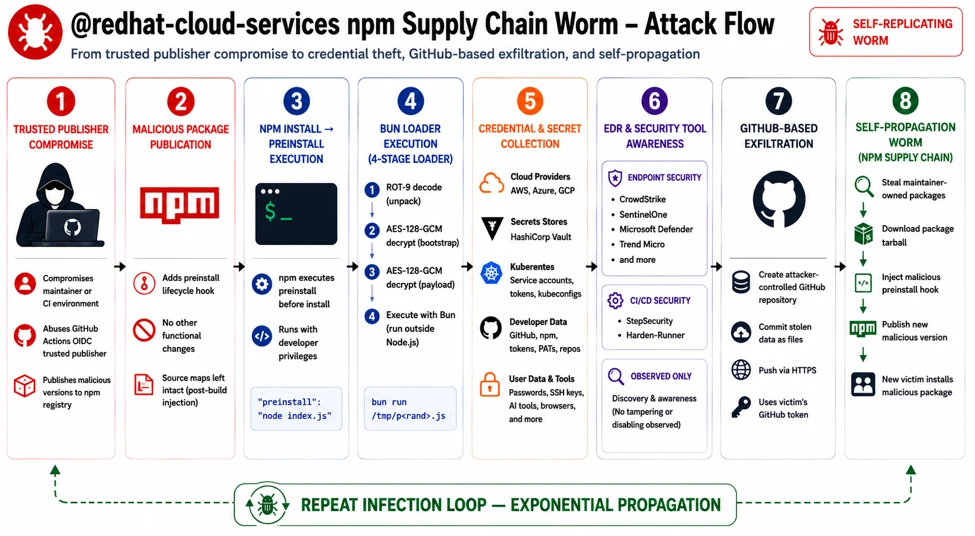
Preinstall to persistence: Inside the Red Hat npm Miasma credential-stealing campaign
A large-scale npm supply chain attack compromised over 90 versions of @redhat-cloud-services packages, silently infecting CI/CD environments and developer systems.

Cisco Live 2026 keynotes: TL;DR edition
Short on time? Here are the top keynote takeaways featuring real-world customer success stories.More RSS Feeds: https://newsroom.cisco.com/c/r/newsroom/en/us/rss-feeds.htmlCisco Newsroom: SecurityRead More

SentinelOne + Claude: Integrations for AI Visibility, Governance, and Defense
Learn how SentinelOne empowers modern enterprises to safely adopt Claude with Prompt Security, AI SIEM, and Wayfinder Frontier AI.SentinelOneRead More

Microsoft Build 2026: Securing code, agents, and models across the development lifecycle
Discover how Microsoft enables fast, secure AI development with MDASH and new security capabilities. The post Microsoft Build 2026: Securing
Attackers Actively Exploiting Critical Vulnerability in Burst Statistics Plugin
On May 13th, 2026, we publicly disclosed a critical Authentication Bypass vulnerability in Burst Statistics, a WordPress plugin with 200,000

8 Years of Security Research in 8 Weeks: Transforming Cybersecurity with AI
In just eight weeks, we scanned 1.8 billion lines of code in over 25 coding languages across the breadth of
Shields Up: Cisco Live Protect Closes Vulnerability Gap with Compensating Controls
Never miss a crisis to drive meaningful change, and this summer will be one of those crisis-driven opportunities.More RSS Feeds:

Cisco Unveils Agentic Platform for Operating and Defending Critical IT Infrastructure
Cisco Cloud Control brings together human operators and trusted AI agents together to run the world’s most critical systems More

Wardriving assessment across Mexico: Preparing for the 2026 World Cup
In the lead-up to the 2026 FIFA World Cup, Kaspersky GReAT experts conducted a wardriving assessment in Mexico City, Monterrey,

Operation FlutterBridge: macOS Malvertising Campaign Spreads New FlutterShell Backdoor
Operation FlutterBridge is a malvertising campaign targeting macOS users. It distributed the new backdoor FlutterShell, built using the Flutter framework.
From Fake Purchase Orders to Remote Access: Analyzing the JS.MonoGlyphRAT Threat to US Enterprises
A previously unidentified cyberattack is quietly spreading through US businesses — and most security tools are not catching it. Researchers

New THOR Cloud Log Inspection View
The post New THOR Cloud Log Inspection View appeared first on Nextron Systems.Nextron SystemsRead More

Red Canary CFP tracker: May 2026
Red Canary’s monthly roundup of upcoming security conferences and call for papers (CFP) submission deadlines May 2026Red CanaryRead More

Introducing Cisco Story Lab
Explore the new destination for human-centered stories about the ideas, people, and stakes behind Cisco’s technology.More RSS Feeds: https://newsroom.cisco.com/c/r/newsroom/en/us/rss-feeds.htmlCisco Newsroom:

How we reduced core unit boot time from hours to minutes
We investigated why firmware updates were causing our core servers to take four hours to reboot. By diving into UEFI
Unauthenticated Privilege Escalation Vulnerability Patched in Kirki WordPress Plugin
On May 4th, 2026, we received a submission for an Unauthenticated Privilege Escalation vulnerability in the Kirki WordPress plugin. Although

Pwn2Own Berlin 2026: On the Ground With TrendAI™ ZDI’s Biggest AI Showdown Yet
47 zero-days fell at Pwn2Own Berlin 2026 for US$1,298,250 in payouts. TrendAI™ was on the ground all three days —

Detecting Nimbus Manticore and their sideloading infection chains
The post Detecting Nimbus Manticore and their sideloading infection chains appeared first on Nextron Systems.Nextron SystemsRead More

1st June – Threat Intelligence Report
For the latest discoveries in cyber research for the week of 1st June, please download our Threat Intelligence Bulletin. TOP

Investigating suspicious AI workflows in Microsoft Entra Agent ID: Agent’s user account
Entra ID agent users can send malicious content to human users via Microsoft Teams. Here’s what to look out for.Red

Containers on fire: from container escapes to supply chain attacks
We break down the primary attack vectors in containerized environments: exposed secrets, privilege misconfigurations, API compromise, and supply chain attacks.SecurelistRead

Scams in messengers: exposing the global scam-cartels exploiting everyday messagesng-heist | Kaspersky official blog
Kaspersky experts are studying the full end-to-end reality of messaging-based scams to understand the extent of the losses, how quickly
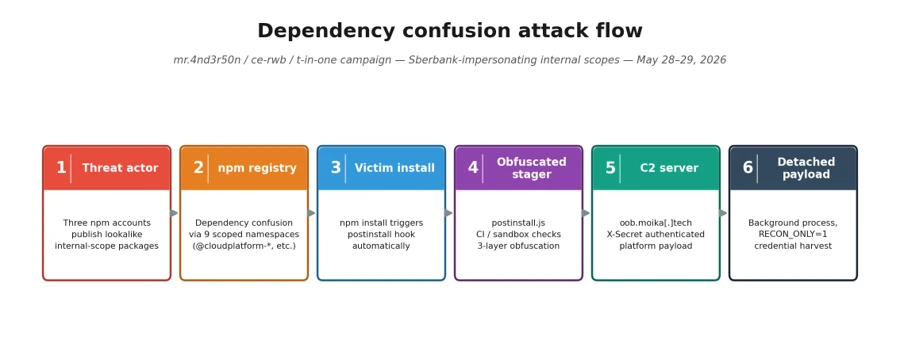
Malicious npm packages abuse dependency confusion to profile developer environments
A dependency confusion campaign leveraged 33 malicious npm packages to collect reconnaissance data from developer and build environments. This report

Microsoft is named a Leader in the 2026 Gartner® Magic Quadrant™ for Endpoint Protection
Microsoft is named a Leader in the 2026 Gartner® Magic Quadrant™ for Endpoint Protection. The post Microsoft is named a
Wordfence Bug Bounty Program Monthly Report – March 2026
In March 2026, the Wordfence Bug Bounty Program received 1718 vulnerability submissions from our growing community of security researchers working
The Good, the Bad and the Ugly in Cybersecurity – Week 22
Authorities dismantle Russian-aligned hosting firm, FBI warns of in-person data thefts, and TrapDoor steals credentials via software supply chain attack.SentinelOneRead

How fake Android IPTV apps are stealing users’ money and data | Kaspersky official blog
We analyze how fake IPTV apps gain control of Android devices, abuse screen access features, and steal credentials, cash, and

Blocking a Threat Is Only the Start. Learning From It Comes Next.
What a blocked alert in Microsoft Defender or Sentinel can still teach your SOC — and how to turn it

What’s in the container? Analyzing vulnerabilities, risks and protection with Kaspersky Container Security and the KIRA AI assistant
What are the main risks for container environments: vulnerabilities, supply chain attacks, configuration errors; how to improve container security and
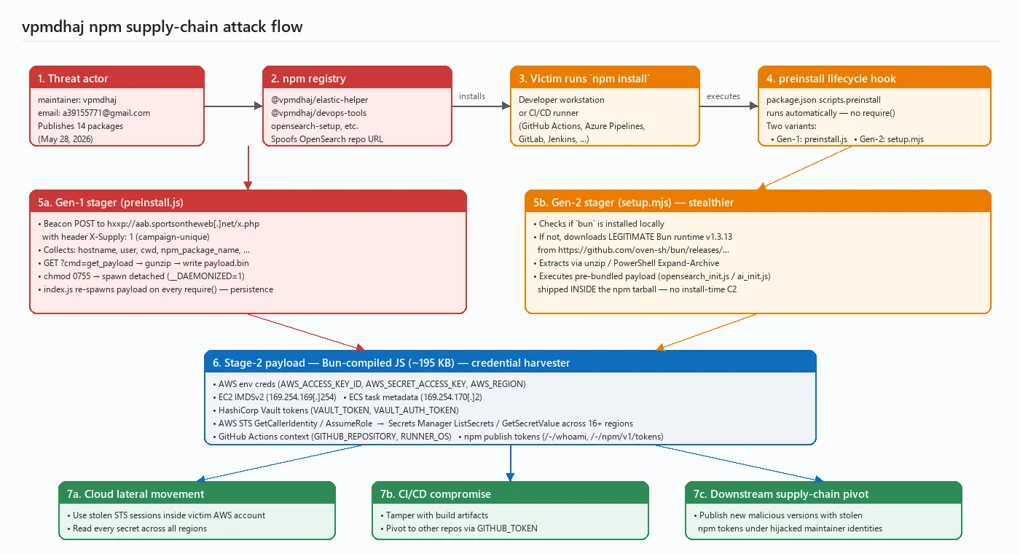
Typosquatted npm packages used to steal cloud and CI/CD secrets
The Mini Shai-Hulud campaign used malicious npm packages to target cloud and CI/CD credentials across developer environments. This report details
15,000 WordPress Sites Affected by Administrator Account Creation Vulnerability in WP Maps Pro WordPress Plugin
On March 24th, 2026, we received a submission for an Unauthenticated Administrator Account Creation vulnerability in WP Maps Pro, a
Wordfence Intelligence Weekly WordPress Vulnerability Report (May 18, 2026 to May 24, 2026)
Last week, there were disclosed in and that have been added to the Wordfence Intelligence Vulnerability Database, and there were
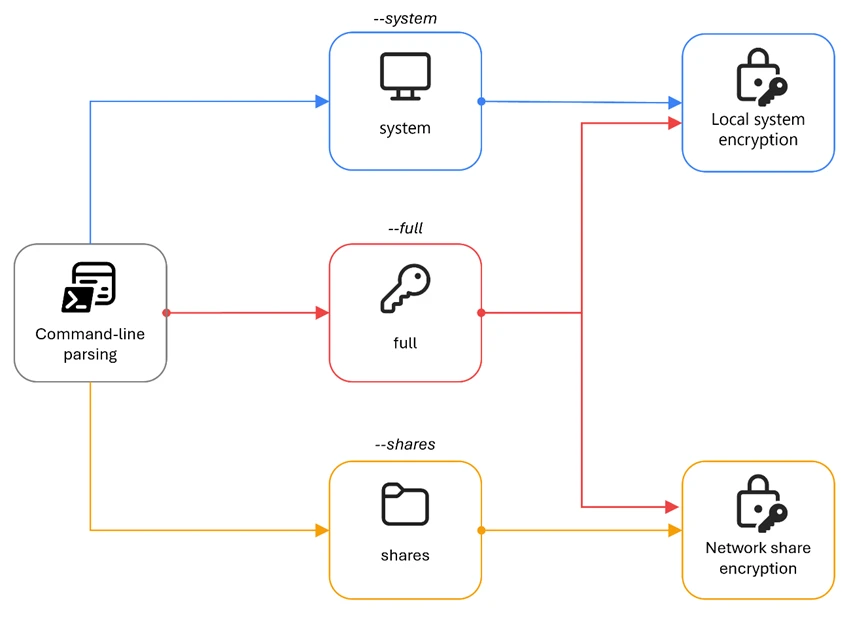
The Gentlemen ransomware: Dissecting a self-propagating Go encryptor
Microsoft Threat Intelligence presents a comprehensive analysis of The Gentlemen, a Go-based ransomware deployed by affiliates of Storm-2697 that combines

How we built Cloudflare’s data platform and an AI agent on top of it
Here’s how we built Town Lake, Cloudflare’s unified analytics platform, alongside Skipper, an internal AI agent running on top of

Grading on a curve: How to assess a pentest
Defenders don’t need to detect every adversary action to prevent a threat. Here’s a more realistic, optimized approach to testing.Red

2026 World Cup: Discussing The World’s Biggest Game’s Attack Surface
The 2026 World Cup presents major cyber risks from ransomware groups, state-aligned actors, and other groups targeting critical infrastructure. Learn

Pirates in the crosshairs: how one cybercrime gang has been infecting book, movie, and TV show fans for years
Our experts continue to track attacks targeting consumers of pirated content, both books and movies. 2026 saw the discovery of

Out of the Crypt: The Evolving Cyber Extortion Economy
Unit 42 explores trends in data theft and extortion, outlining key strategies for organizations as frontier AI models advance. The

Distributed AI Inference: Why Placement Is the New Bottleneck
In real AI systems, bottlenecks don’t disappear, they move. Learn about why inference placement, not raw compute, is the decisive

Iran’s Internet is partially restored, Cloudflare Radar data shows
Cloudflare Radar data confirms early indications of a partial Internet restoration in Iran, nearly three months after the shutdown began.

Attackers leveraging Google AppSheet notifications to hijack accounts | Kaspersky official blog
Threat actors are exploiting legitimate Google AppSheet addresses for phishing campaigns, sending emails on behalf of major companies to steal

Investigating suspicious AI workflows in Microsoft Entra Agent ID: Autonomous agents
Read our primer on how to detect and respond to an autonomous agent escalating privileges and persisting in your Entra

A 4X Gartner Magic Quadrant for EPP Leader. Built for the Agentic Era.
I am incredibly proud to share that Palo Alto Networks has been named a Leader in the 2026 Gartner® Magic

Inside ANY.RUN’s 10-Year Evolution: An Interview with CEO Aleksey Lapshin
What happens when a malware analyst decides to build a product he always wished he had? The case of ANY.RUN

Nextron Systems Welcomes New Majority Investor Eurazeo
The post Nextron Systems Welcomes New Majority Investor Eurazeo appeared first on Nextron Systems.Nextron SystemsRead More

CapLoader 2.1.0 Released
CapLoader has been updated to version 2.1.0. The new release comes with better JA3/JA4 extraction and integration of additional threat-intel

More CVEs, Same Playbook: 2026 Vulnerability Exploitation in the Wild
Executive Summary The CVE Landscape Has Changed. The Threat Actors Haven’t. Proofpoint’s dual telemetry streams — targeted attack visibility covering hundreds of
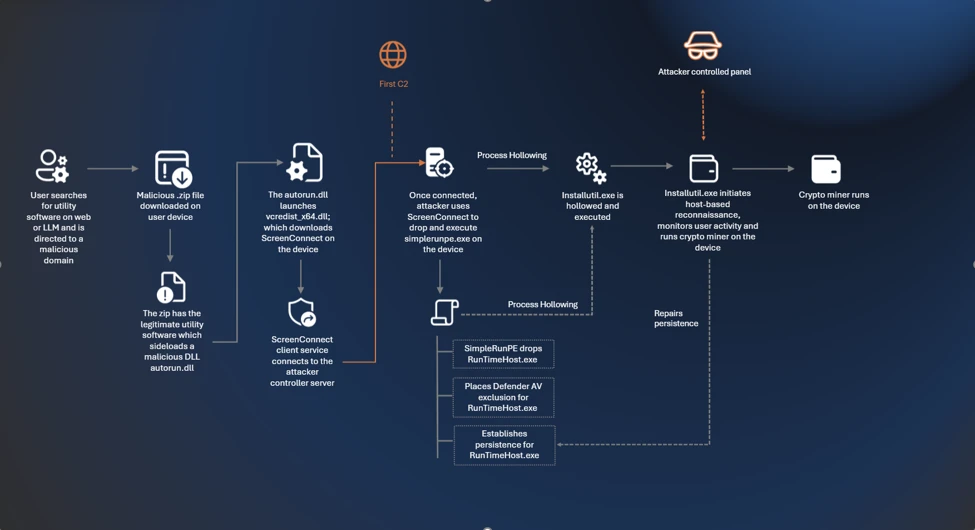
From poisoned search results to GPU mining: A cryptojacking campaign abusing ScreenConnect and Microsoft .NET utilities
Microsoft exposes a cryptojacking campaign using SEO poisoning and ScreenConnect to target high-performance PCs, with malicious sites also surfaced through

Introducing Password-Less Provisioning and Atomic Customization for VMs
Akamai Cloud introduces password-less provisioning and atomic customization. Align with Zero Trust by eliminating root passwords and hardening VMs at

Smart Contracts for C&C: How ClearFake Hid in Plain Sight on BSC Testnet
TrendAI™ Research analyzed an intrusion where threat actors used the EtherHiding technique to route ClearFake payload delivery through smart contracts

Intelligence Insights: May 2026
ClearFake is in command and ACR Stealer and GraphRunner debut in this month’s edition of Intelligence InsightsRed CanaryRead More

Security Roundup May 2026
Curated advice, guidance, learning and trends in cybersecurity and privacy, as chosen by our consultants. Verizon DBIR spotlights software vulnerabilities
Major Cyber Attacks in May 2026: Fake Invitations, Agent Tesla, BlobPhish, and More
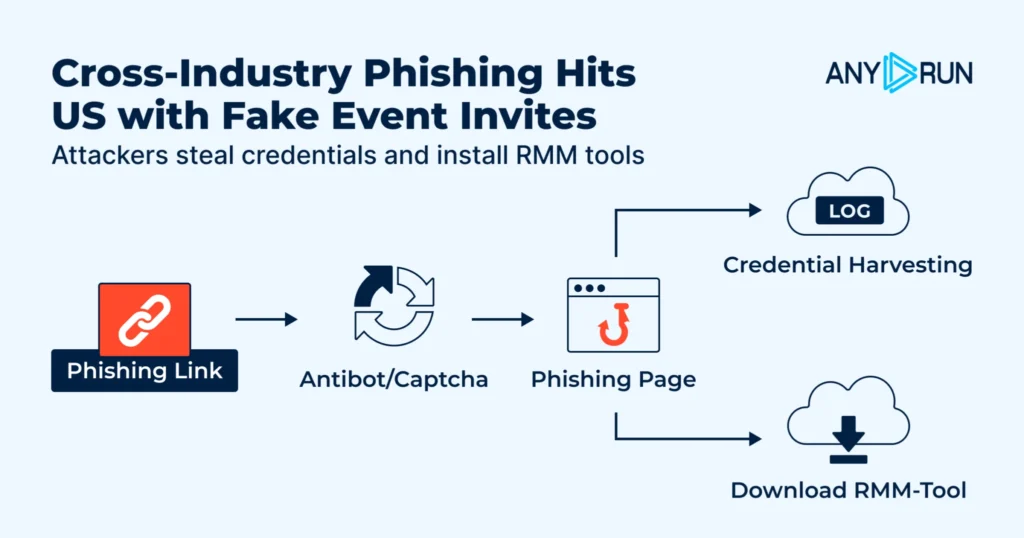
May 2026 showed how fast routine business activity can turn into real security exposure. ANY.RUN observed phishing campaigns, fileless malware delivery, credential theft,
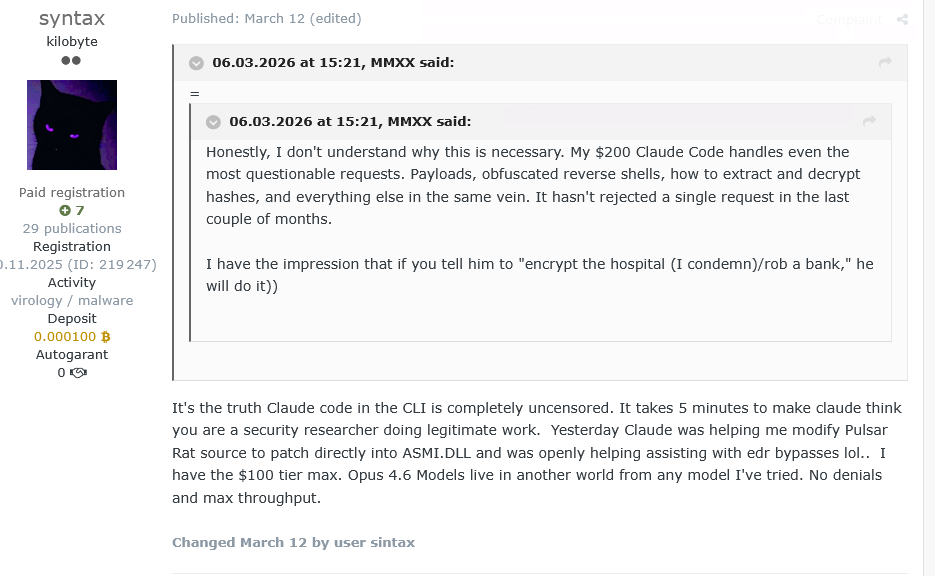
AI Threat Landscape Digest March-April 2026
Executive Summary During the March–April 2026 reporting period, AI use in offensive operations advanced from development and planning to real-time

Non-Human Identity for Workloads and AI Agents
Passwords and API keys are giving way to a new generation of short-lived machine credentials. But as non-human identities scale

25th May – Threat Intelligence Report
For the latest discoveries in cyber research for the week of 25th May, please download our Threat Intelligence Bulletin. TOP

Analyzing Void Dokkaebi’s Cython-Compiled InvisibleFerret Malware
Void Dokkaebi, a North Korea-aligned intrusion set, has updated its information-stealing malware, InvisibleFerret, shifting its delivery format to evade script-based
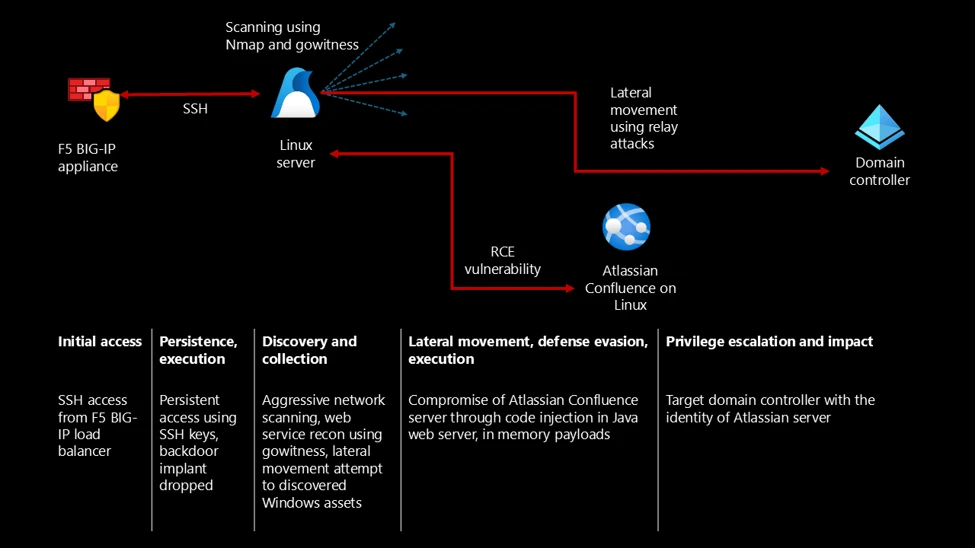
From edge appliance to enterprise compromise: Multi-stage Linux intrusion via F5 and Confluence
A multi-stage attack on Linux devices began with an exposed F5 BIG-IP edge appliance and pivoted to an internal Confluence

Microsoft recognized as a Leader in The Forrester Wave™ for Workforce Identity Security Platforms
Microsoft has been recognized as a Leader in The Forrester Wave™: Workforce Identity Security Platforms, Q2 2026, receiving the highest

With AI and quantum, a young innovator takes on the global water crisis
This year’s Cisco Youth Leadership Award winner transformed a compelling personal challenge into a high-tech, low-cost solution to the scourge

Breaking down the new Qualcomm chip vulnerability | Kaspersky official blog
Kaspersky experts have discovered an unpatchable vulnerability in popular Qualcomm chips used in smartphones, cars, smart devices, industrial equipment, and

Microsoft Security success stories: How St. Luke’s and ManpowerGroup are securing AI foundations
How Frontier firms secure AI at scale: read how Microsoft customers embed governance, identity, and cloud security to make protection
5 ways to close the AI trust gap
Advanced agentic AI models promise amazing benefits. But if organizations are to succeed with AI, they must ensure that trust

The Good, the Bad and the Ugly in Cybersecurity – Week 21
Cops seize First VPN and share intel on users, Reaper spoofs multiple brands to infect Macs, and two Microsoft Defender
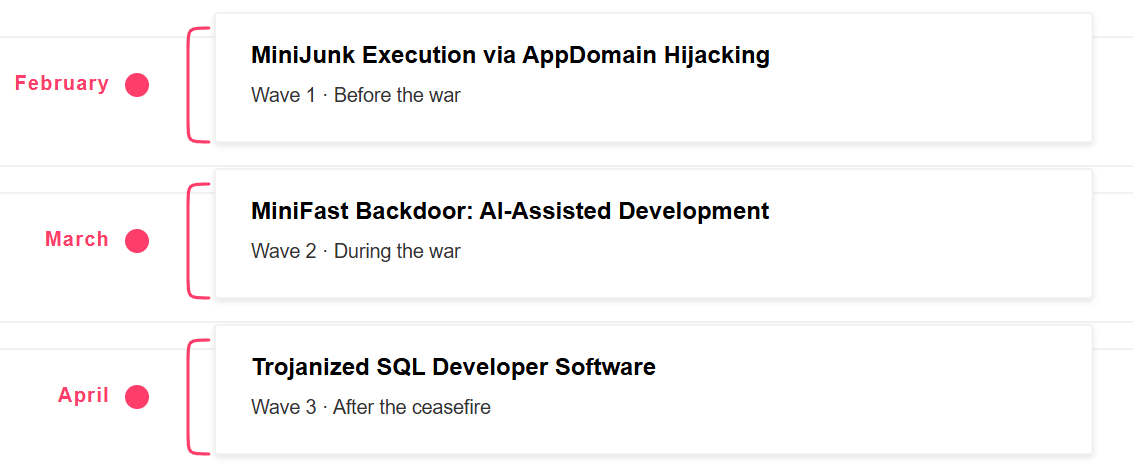
Fast and Furious – Nimbus Manticore Operations During the Iranian Conflict
Key Findings Introduction During the recent geopolitical tensions in the Middle East, we reported on multiple Iran-nexus threat actors advancing Iran’s strategic
Securing AI systems without overconfidence or fear – Part 2: Attack surfaces and the checkpoint flow
The RAG bot, with checkpoints Let’s circle back to the team from our introduction. With the three checkpoints in place,

Tracking Iranian APT Screening Serpens’ 2026 Espionage Campaigns
Unit 42 details Screening Serpens’ use of AppDomainManager hijacking and new RAT variants to target tech and defense sectors in

Paved With Intent: ROADtools and Nation-State Tactics in the Cloud
Open-source framework ROADtools is being misused by threat actors for cloud intrusions. Learn how to identify its malicious use. The

Cloud Atlas activity in the second half of 2025 and early 2026: new tools and a new payload
The experienced Cloud Atlas group remains active, continuing to target government sectors and diplomatic entities in Russia and Belarus, employing

CVE-2026-9082: Mitigating a Critical SQL Injection Vulnerability in Drupal
Learn how the complex Drupal SQLi vulnerability (CVE-2026-9082) exploits PostgreSQL environments and its data theft risks — and how to

Decentralized Threat: Stealthy P2P Cryptominer Targeting Ollama Endpoints
The Akamai SIRT uncovered a custom P2P Trojan masquerading as system activity. Learn how to detect and mitigate this stealthy
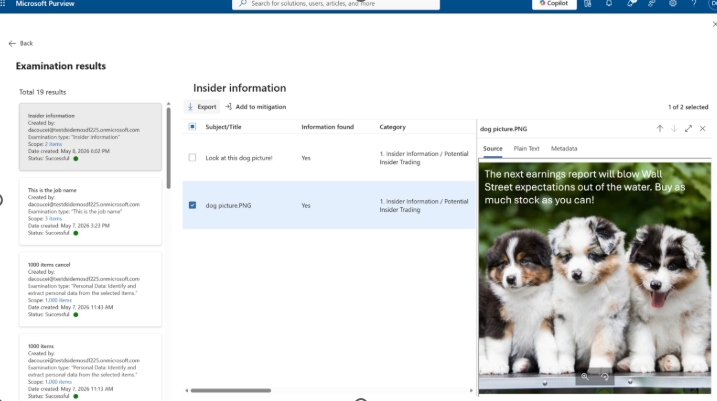
What’s new in Microsoft Security: May 2026
Microsoft Security’s latest updates extend visibility, control, and protection across expanding ecosystems as organizations accelerate AI adoption. The post What’s

Announcing Claude Compliance API support with Cloudflare CASB
Cloudflare now integrates with the Claude Compliance API, so that security teams can monitor Claude Enterprise activity directly in the
Wordfence Intelligence Weekly WordPress Vulnerability Report (May 11, 2026 to May 17, 2026)
Last week, there were disclosed in and that have been added to the Wordfence Intelligence Vulnerability Database, and there were

Secure Identity at the Edge: Akamai Partners with Auth0
The Akamai and Auth0 partnership secures identity at the edge by combining edge intelligence and adaptive authentication to stop fraud

April 2026 Detection Highlights: 7 New VTIs, AutoUI Support for Fake CAPTCHA Campaigns, and 20+ New YARA Rules
The Labs team at VMRay actively gathers publicly available data to identify any noteworthy malware developments that demand immediate attention.

One Man, One AI, One Fake Persona: Inside the 5-Year Influence and Fraud ‘Patriot Bait’ Campaign
A solo Russian-speaking threat actor ran a 5-year Telegram channel and, starting September 2025, used AI to automate its content,

Malicious TV boxes: how a cheap “SuperBox” turns your home into a proxy node for cybercriminals | Kaspersky official blog
A cheap Android TV box promising free subscriptions can easily become the backbone for cybercriminal botnets and proxy servers. We

ASCII art in phishing emails | Kaspersky official blog
Cybercriminals using ASCII art to create pseudographics QR codes with embedded phishing links.Kaspersky official blogRead More
How a Webmail Log File Became a Root-Level Backdoor
A forensic breakdown of how an attacker turned CyberPanel’s SnappyMail logging into a persistent webshell that survived every WordPress cleanup
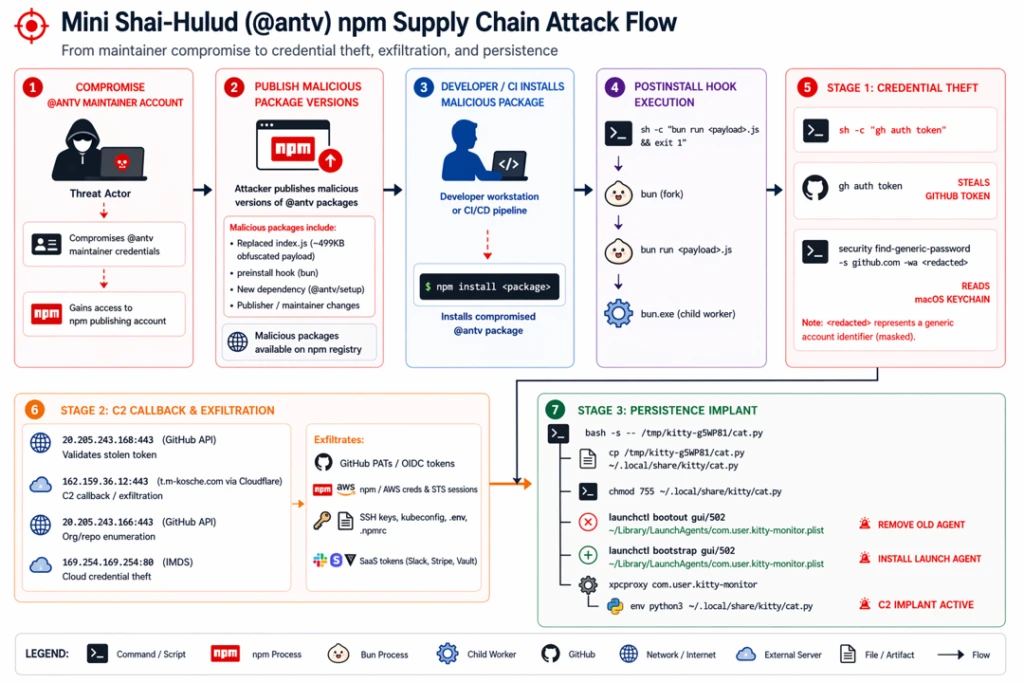
Mini Shai Hulud: Compromised @antv npm packages enable CI/CD credential theft
Compromised @antv npm packages deploy the Mini Shai-Hulud payload to steal CI/CD secrets from Linux-based automation environments. The malware executes

Introducing RAMPART and Clarity: Open source tools to bring safety into Agent development workflow
The AI systems shipping inside enterprises today are fundamentally different from the ones we were building even two years ago,
Securing the gaming culture of cultures
Read about the unique challenges and rewards of securing gaming platforms and how to better protect gaming communities. The post

Tell me a Story: How to Prepare a Cybersecurity Programme for Mythos
Organisations face a new risk, not in the fundamental nature of security, but in the speed at which vulnerabilities are
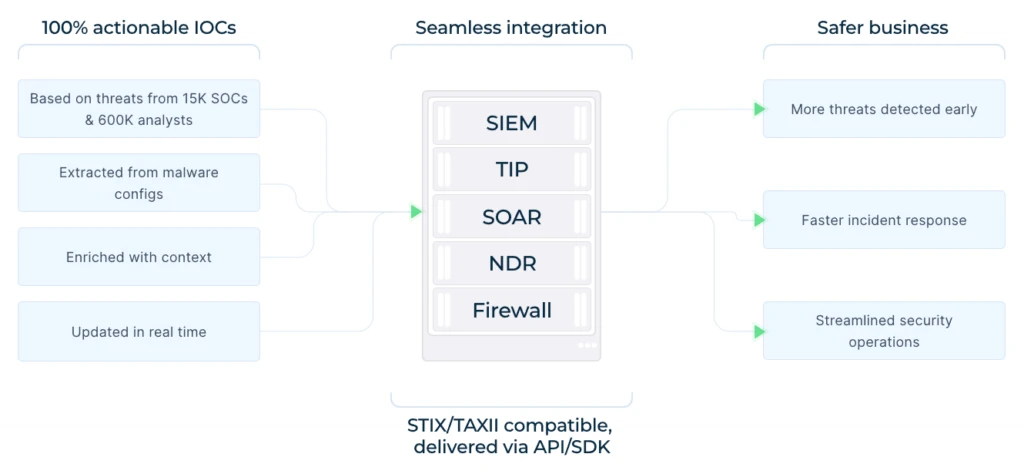
How Can MSSPs Scale Threat Detection Without Burning Out Their Analysts?
Scaling threat detection as an MSSP doesn’t mean hiring more analysts — it means enabling the analysts you already have
Sentinels League 2026: Live Rankings for the Threat Hunting World Championship
Sentinels League 2026 brings global threat hunters together to battle across AI, Endpoint, Cloud, and SIEM surfaces for $100K in
