Some of Europe’s most wanted fugitives are still at large despite being sentenced to years in prison for serious crimes.
Blogs from all around the World
Recent blog posts

Cybercriminal VPN used by ransomware actors dismantled in global crackdown
For years, the service, known as ‘First VPN’, was promoted on Russian-speaking cybercrime forums as a trusted tool for remaining

Two dangerous fugitives arrested in Türkiye and Spain
Two dangerous fugitives wanted for serious organised crime offences have been arrested in separate international operations.One suspect, wanted by Germany

Europol supports international hit against counterfeit medicines and supplements network
The criminal organisation, comprising individuals from Romania, the Republic of Moldova, Bulgaria, Estonia, Poland, and Ukraine, has been operating for

EU targets Iran’s Revolutionary Guard propaganda ecosystem in an online crackdown
A total of 14 200 posts linked to Iran’s Islamic Revolutionary Guard Corps (IRGC), now designated as a terrorist organisation

Swedish fugitive arrested as new OTF GRIMM targets added to EU Most Wanted
The arrested individual, a man in his 30s linked to the Foxtrot network, was wanted by Swedish authorities for murder,
Latest

Microsoft dismantles Fox Tempest cybercrime platform tied to ransomware attacks on hospitals, critical organizations
New Microsoft research disclosed disruption of a cybercrime operation known as Fox Tempest, a malware-signing-as-a-service (MSaaS) platform that… The post

EU Most Wanted platform helps locate Hungarian child abuser hiding in Spain
The 37-year-old man was arrested in Tenerife on 7 May, three days after his profile was published on the platform.

Atlantic ‘Cocaine Highway’ broken in coordinated maritime operation
Between 13 and 26 April 2026, law enforcement targeted criminal networks moving cocaine from Latin America to Europe through complex

Europol announces transition arrangements following the departure of Executive Director Catherine De Bolle
As from 2 May, Europol has entered into a transition phase with specific arrangements following the departure of Executive Director

“Terrorgram” network dealt another blow as member sentenced in Denmark
A Danish-French national has been sentenced to six years in prison for terrorism-related offences by the District Court in Glostrup,

Call centres dismantled and ten arrested in EUR 50 million online fraud case
A criminal network operating a large-scale online fraud scheme has been dismantled through a collaborative investigation involving Austrian and Albanian

OTF GRIMM one-year anniversary: violence-as-a-service targets published on EU Most Wanted
As the Operational Taskforce (OTF) GRIMM marks its first year of activity, high-value targets linked to ongoing investigations are being

Europol supports hit against ‘Black Axe’ criminal organisation in Switzerland: 10 arrests
Europol has supported a comprehensive investigation conducted by Swiss authorities in collaboration with German law enforcement against members of the

New 2026 ‘IOCTA’ highlights sophisticated tactics and emerging challenges in the digital landscape
Europol today published the new edition of the Internet Organised Crime Threat Assessment (IOCTA) 2026, providing an in-depth analysis of

Child sexual exploitation: 12 children identified during Europol’s Victim Identification Taskforce
From 13 to 24 April 2026, 34 specialists in victim identification from Europol, INTERPOL and 31 countries worldwide gathered at

Bluesky Disrupted by Sophisticated DDoS Attack
A pro-Iran hacker group has taken credit for the attack on Bluesky, which appears to have lasted 24 hours. The

Is “Satoshi Nakamoto” Really Adam Back?
The New York Times has a long article where the author lays out an impressive array of circumstantial evidence that

Hackers Abuse QEMU for Defense Evasion
The machine emulator has been abused in at least two different campaigns distributing ransomware and remote access tools. The post

Mining China’s ‘Little Red Book’ for Open Source Gold
The challenges of conducting open-source research in China are well-documented. Consistently named one of the most digitally oppressive countries in

British Scattered Spider Hacker Pleads Guilty in the US
Tyler Buchanan admitted in court to hacking into various companies, defrauding them, and stealing cryptocurrency from multiple individuals. The post

Mythos: An AI tool too powerful for public release
Anthropic is keeping Mythos out of public hands, with limited access for select organizations over fears it could be misused.MalwarebytesRead

Big Tech can stop scams. They just don’t (Lock and Code S07E08)
This week on the Lock and Code podcast, we speak with Marti DeLiema about what really works in protecting older

Serial-to-IP Converter Flaws Expose OT and Healthcare Systems to Hacking
Forescout researchers discovered 20 new vulnerabilities in Lantronix and Silex products and described theoretical attack scenarios. The post Serial-to-IP Converter

Why We Actually Need End-to-End Encryption
There is a certain kind of argument that appears every time encryption comes up. Yes, yes, privacy is lovely. But

Europol and partners track down 45 forcibly transferred Ukrainian children
On 16 and 17 April 2026, Europol together with the Netherlands hosted a coordinated effort to identify and trace children

Europol-supported global operation targets over 75 000 users engaged in DDoS attacks
On 13 April 2026, 21 countries joined forces in a coordinated action week that focused on enforcement and prevention measures

Leading Balkan Cartel member arrested in Montenegro
On 15 April 2026, Europol supported law enforcement authorities in Montenegro in conducting a large-scale operation targeting a significant cell

Spain: 24 arrested in crackdown on speedboat migrant smuggling network
The suspects, who are Algerian, Moroccan, and Spanish nationals, maintained the migrant smuggling network’s strong presence in Almería, Spain. While

Five-country operation targets cigarette smuggling network operating from the UK
Investigation began with major seizure in ItalyThe investigation was launched in September 2024 following the seizure of 12 million counterfeit

The grip on migrant smuggling tightens: new department at Europol to step up the fight
Today, Europol has launched its new European Centre Against Migrant Smuggling (ECAMS), stepping up the European Union fight against migrant

Central Mediterranean: 10 migrant smugglers targeted
On 18 and 19 March 2026, Europol hosted a digital action day under a dedicated Joint Team targeting migrant smugglers

A legal vacuum on CSAM detection puts children at greater risk
The removal of the current legal basis enabling voluntary detection by online platforms could have far-reaching implications for safeguarding children.Last

Small boats supply chain disrupted: 21 arrested for supplying Channel smugglers with nautical equipment
A joint investigation conducted under the framework of a Europol task force resulted in a significant disruption of the migrant

From intelligence to conviction: Europol helps dismantle Terrorgram Collective
A Canadian man has been sentenced by the Public Prosecution Service of Canada to 20 years in prison for terrorism-related

Guns-for-cannabis network hit: Europol high-value target arrested in international action
The main suspect, a Turkish national holding a Greek residence permit, is believed to have coordinated the sourcing and transport

Major operation targets one of Scotland’s most violent crime networks
Violence, drugs and controlThe gang is known for using violence to dominate territory and protect its criminal activity. Investigators believe

From Vietnam to the EU by air: 8 arrested in a migrant smuggling sting across Europe
On 30 March 2026, a coordinated international French-led operation, which was supported by Europol and involved law enforcement and judicial

Up to EUR 50 000 for a passage to the UK: 19 suspected migrant smugglers arrested
On 30 March 2025, Europol supported an action day against criminal networks smuggling migrants from Vietnam to the European Union

Tíz éves a kiberhónap: #ThinkB4UClick!
Az Európai Unió Kiberbiztonsági ügynöksége (az ENISA) 2011-ben kezdett el foglalkozni azzal a gondolattal, hogy egy szervezett kampány keretei között olyan
Sysmon file zárolás
A Sysmon új verziója számos új funkcióval bővült, többek között a file zárolás lehetőségével. Az új funkció lehetővé teszi futtatható
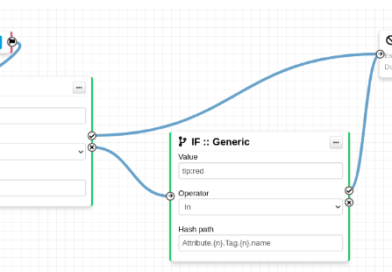
Számos új fukcióval bővült a MISP
A MISP (Malware Information Sharing Platform) új korrelációs motorral, új munkafolyamatokkal bővült a mostani kiadásában. FORRÁS
JSON minden logot
Ha szeretszt Elasticsearch-el dolgozni és szereted, ha a logjaid egységes neveket alkalmaznak, egységes típusokat az a jó megoldás számodra. FORRÁS
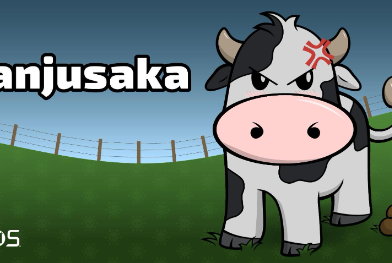
Majnuska: a Coblat Strike kínai kistestvére
Cisco Talos nemrég felfedezett egy új támadó keretrendszert amelyet ‘Manjusaka’-nak neveznek.A kutatás egy rosszindulatú Word dokumentum elemzésével kezdődött, amiben egy

Virustotal kutatás a rosszindulatú kódok által használt megtévesztési formákról
A jelentés fókusza a megtévesztési formákra fókuszál, így biztosítva tisztább összképet arról, hogy a rosszindulatú kódok fejlesztői milyen formában igyekeznek

Új malware a SolarWinds támadóitól
A SolarWinds supply chain támadás mögött álló csoport tovább fejlesztette eszközeinek arzenálját egy új eszközzel, amelyet már 2019 óta észrevétlenül
Protonmail megosztja a felhasználók IP címeit?
A ProtonMail kritikák célpontjává vált, amikor egy, Franciaországból az EUROPOLON keresztül érkező jogsegély kérés alapján megosztotta egy aktivista IP címét
Fegyverrendszerek sebezhetősége
Az alábbi idézettel kezdi bejegyzését Bruce Schneier a blogján: “Ha úgy gondolod, hogy a rendszereid az elvártaknak megfelelően fognak működni egy háború során, akkor csak hülyét csinálsz magadból”
A 21. századi konfliktusok a kiber műveleteket is magukban hordozzák. Fegyver- és logisztikai rendszerek is célpontok lesznek, így karabélyok, pisztolyok drónok vagy kórházak nem fognak működni, vagy az utánpótlás nem érkezik meg időben.
Az elmúlt évtizedben számos ország építette fel a kiber parancsnokságát, fogadott el kiber doktrínát. De a beszélgetésnek nem szabad csak a támadási képességre koncentrálnia. Ha úgy vásárolunk új fegyvereket felszereléseket és építünk ki új képességeket, hogy azokat nem tudjuk megvédeni, az olyan mintha megvennénk a legjobb puskát majd azt egy őrizetlen lezáratlan szekrénybe tennénk.


