Iranian threat group Boggy Serpens’ cyberespionage evolves with AI-enhanced malware and refined social engineering. Unit 42 details their persistent targeting.
Vendors' News
Vendor announcements

Cisco Secure AI Factory: powering agentic AI at scale
Cisco’s integrated tech stack—from silicon to software—powers secure, scalable enterprise AI adoption.More RSS Feeds: https://newsroom.cisco.com/c/r/newsroom/en/us/rss-feeds.htmlCisco Newsroom: SecurityRead More

New Microsoft Purview innovations for Fabric to safely accelerate your AI transformation
As organizations adopt AI, security and governance remain core primitives for safe AI transformation and acceleration. The post New Microsoft

Standing up for the open Internet: why we appealed Italy’s “Piracy Shield” fine
Cloudflare is appealing a €14 million fine from Italian regulators over “Piracy Shield,” a system that forces providers to block

Iranian Cyber Threat Evolution: From MBR Wipers to Identity Weaponization
The evolution of Iranian cyber operations in broad context: from custom wiper malware to misuse of legitimate admin tools and

Help on the line: How a Microsoft Teams support call led to compromise
A DART investigation into a Microsoft Teams voice phishing attack shows how deception and trusted tools can enable identity-led intrusions

16th March – Threat Intelligence Report
For the latest discoveries in cyber research for the week of 16th March, please download our Threat Intelligence Bulletin. TOP

When AI hallucinations turn fatal: how to stay grounded in reality | Kaspersky official blog
A 36-year-old American man took his own life after two months of interacting with Gemini, with the chatbot reportedly pushing

Exclusive interview: Richard Ticho, Executive Producer of The Women In Security Documentary
Our last blog covered The Women In Security Documentary which highlights women’s role in an industry where they have been

Free real estate: GoPix, the banking Trojan living off your memory
Kaspersky GReAT experts describe the unprecedentedly complex Brazilian banking Trojan GoPix that employs memory-only implants, Proxy AutoConfig (PAC) files for

ANY.RUN at RootedCON 2026: Meeting Security Teams and Showcasing New Capabilities
From March 5 to March 7, the ANY.RUN team attended RootedCON 2026 in Madrid and showcase some of our latest capabilities developed for modern SOC environments at the

Web Shells, Tunnels, and Ransomware: Dissecting a Warlock Attack
Warlock continues to enhance its attack chain with new tactics to improve persistence, lateral movement, and defense evasion using an

Announcing Prisma AIRS Availability in Singapore Region
Palo Alto Networks launches Prisma AIRS in Singapore. Get AI-native threat protection, data residency and cyber resilience. The post Announcing
Latest

Gartner suggests Friday afternoon Copilot ban because users may be too lazy to check its mistakes
You’ll be exhausted by then because securing Microsoft’s AI helper is not a trivial task Gartner analyst Dennis Xu has

Gartner suggests Friday afternoon Copilot ban because users may be too lazy to check its mistakes
You’ll be exhausted by then because securing Microsoft’s AI helper is not a trivial task Gartner analyst Dennis Xu has
Ubuntu 24.04 22.04 Linux Kernel NVIDIA Critical Privilege Escalation
Several security issues were fixed in the Linux kernel.LinuxSecurity – Security AdvisoriesRead More
Ubuntu 24.04 LTS USN-8095-2 Linux Kernel Critical Local Escalation
Several security issues were fixed in the Linux kernel.LinuxSecurity – Security AdvisoriesRead More
Ubuntu 22.04 LTS Advisory USN-8096-2 Linux Kernel FIPS Security
Several security issues were fixed in the Linux kernel.LinuxSecurity – Security AdvisoriesRead More
Ubuntu 20.04 curl Critical Authentication Issues USN-8099-1 CVE-2026-1965
Several security issues were fixed in curl.LinuxSecurity – Security AdvisoriesRead More
Ivanti EPMM ‘Sleeper Shells’ not so sleepy?
In late January 2026 an advisory covering two remote code execution vulnerabilities (CVE-2026-1281 & CVE-2026-1340) in Ivanti Endpoint Manager Mobile

From legacy architecture to Cloudflare One
Learn how Cloudflare and CDW de-risk SASE migrations with a blueprint that treats legacy debt as an application modernization project.The

DRILLAPP: new backdoor targeting Ukrainian entities with possible links to Laundry Bear
LAB52, the intelligence team at S2 Group, has identified a new campaign targeting Ukrainian entities, attributed to actors linked to

The Good, the Bad and the Ugly in Cybersecurity – Week 11
Ransomware negotiator charged with aiding BlackCat, actors exploit FortiGate firewalls to breach networks, and Iran hacktivists wipe Stryker systems.SentinelOneRead More
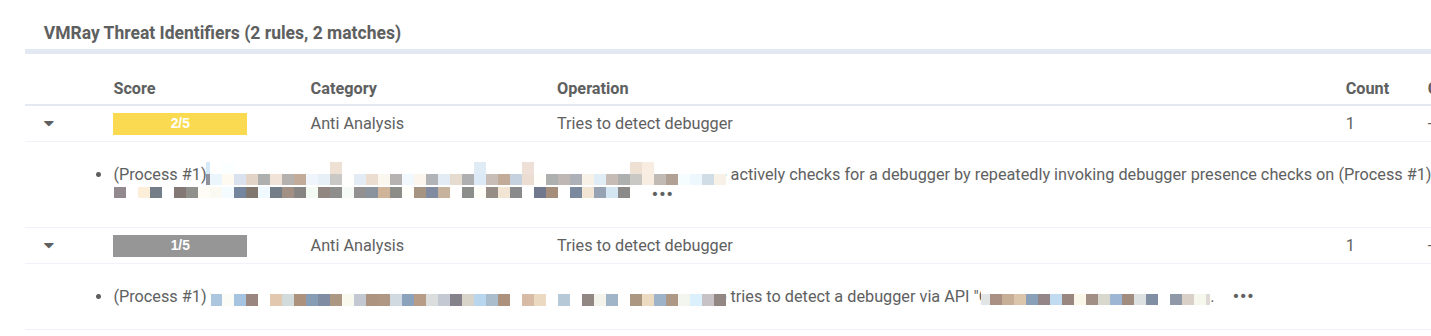
February 2026 Detection Highlights: 8 New VTIs, Expanded Config Extractors, and 30+ Fresh YARA Rules
The Labs team at VMRay actively gathers publicly available data to identify any noteworthy malware developments that demand immediate attention.

RSAC 2026: Tag in a Partner for the AI Security Showdown
Legacy security wasn’t built for autonomous AI. See how Akamai partners are stepping into the ring to build trust and

Suspected China-Based Espionage Operation Against Military Targets in Southeast Asia
An espionage operation demonstrated strategic operational patience against targets in Southeast Asia, deploying custom backdoors. The post Suspected China-Based Espionage
Insights: Increased Risk of Wiper Attacks
We are observing an increase of wiper attacks by the Iran-linked Handala Hack group (aka Void Manticore) through phishing and

AMOS and Amatera disguised as AI agents | Kaspersky official blog
Threat actors are advertising pages featuring malicious instructions for installing AI agents like Claude Code, Doubao, and OpenClaw.Kaspersky official blogRead
Wordfence Intelligence Weekly WordPress Vulnerability Report (March 2, 2026 to March 8, 2026)
Last week, there were disclosed in and that have been added to the Wordfence Intelligence Vulnerability Database, and there were

“Handala Hack” – Unveiling Group’s Modus Operandi
Key Findings Introduction Handala Hack, also tracked by Check Point Research as Void Manticore, is an Iranian threat actor that
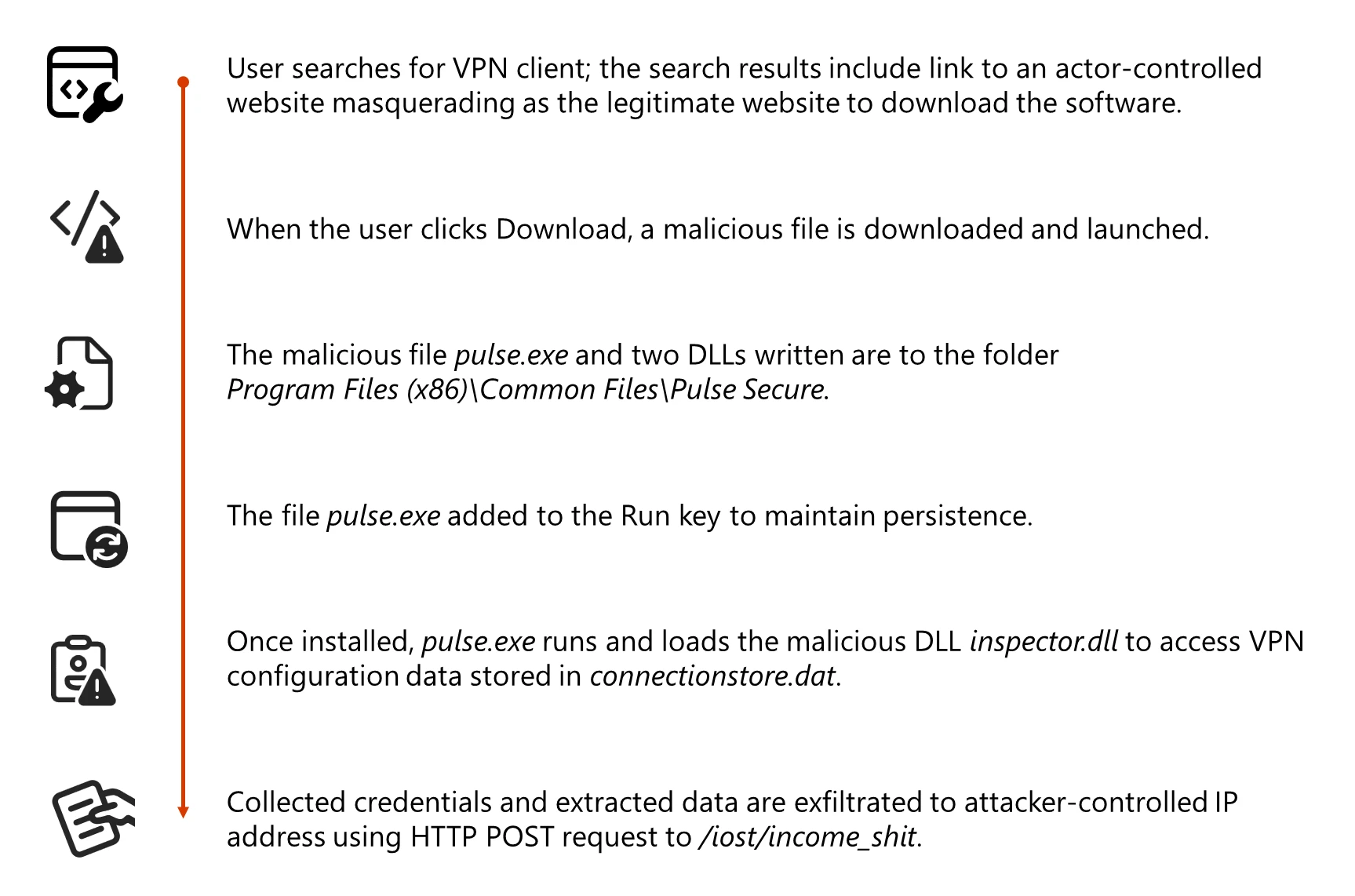
Storm-2561 uses SEO poisoning to distribute fake VPN clients for credential theft
Storm-2561 uses SEO poisoning to push fake VPN downloads that install signed trojans and steal VPN credentials. Active since 2025,
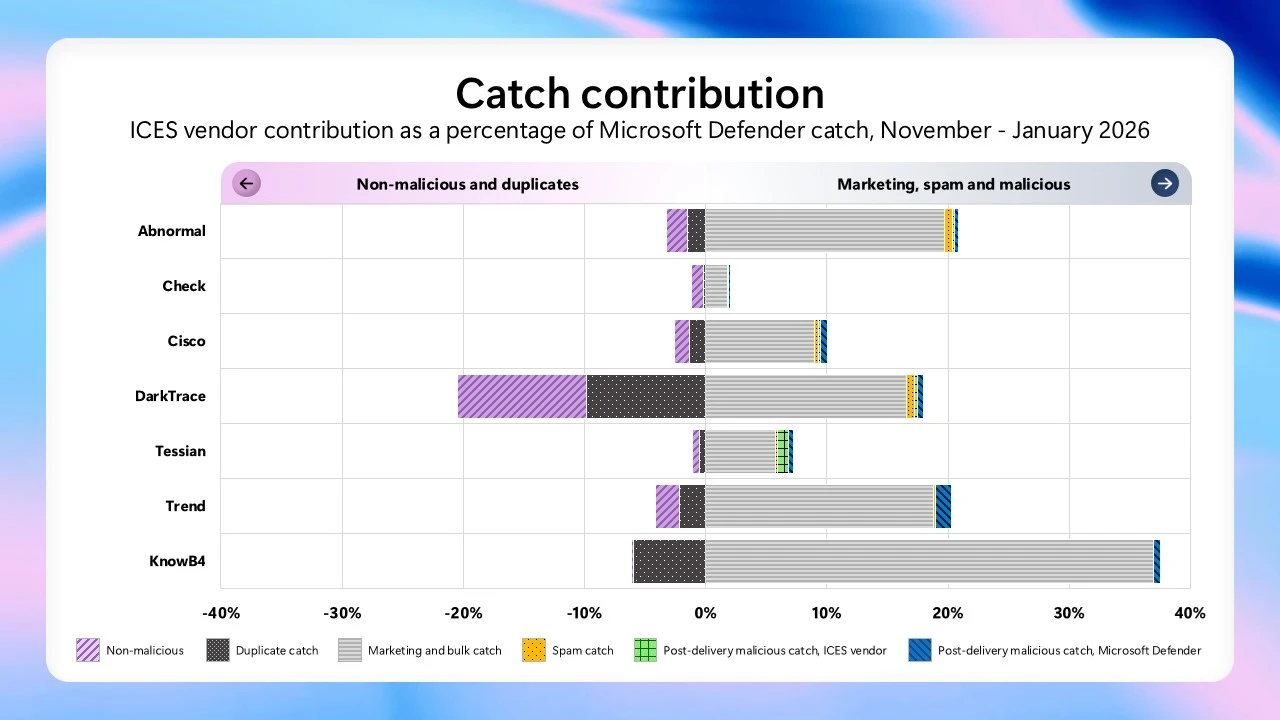
From transparency to action: What the latest Microsoft email security benchmark reveals
The latest Microsoft benchmarking data reveals how Microsoft Defender mitigates modern email threats compared to SEG and ICES vendors. The
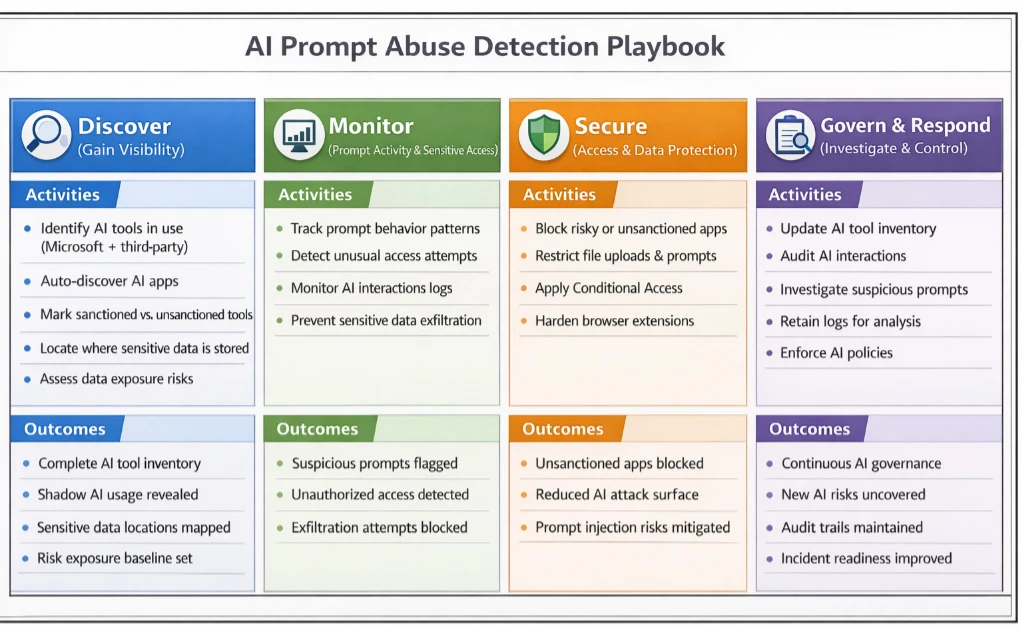
Detecting and analyzing prompt abuse in AI tools
Hidden instructions in content can subtly bias AI, and our scenario shows how prompt injection works, highlighting the need for

Announcing Cloudflare Account Abuse Protection: prevent fraudulent attacks from bots and humans
Blocking bots isn’t enough anymore. Cloudflare’s new fraud prevention capabilities — now available in Early Access — help stop account

Moving up the Assemblyline: Exposing malicious code in browser extensions
How to use the open source Assemblyline tool to track browser extension updates and detect malicious codeRed CanaryRead More

MicroStealer Analysis: A Fast-Spreading Infostealer with Limited Detection
Security teams depend on early signals to spot and contain new threats. But what happens when a fully capable infostealer
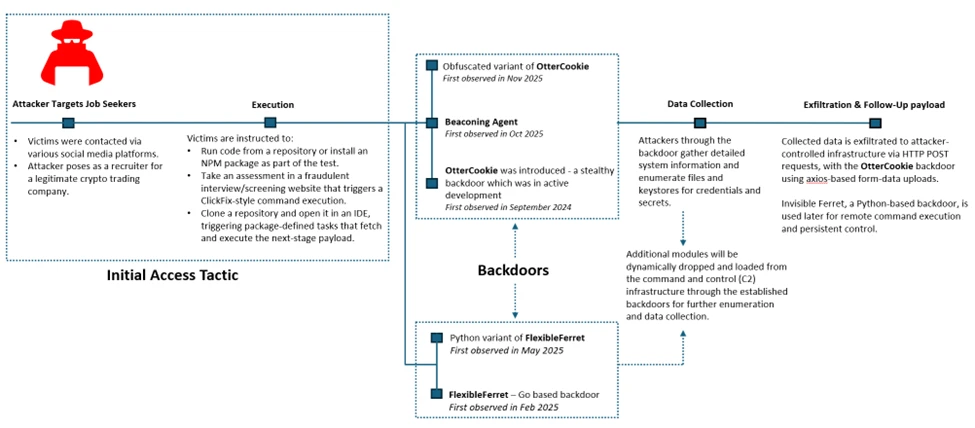
Contagious Interview: Malware delivered through fake developer job interviews
The Contagious Interview campaign weaponizes job recruitment to target developers. Threat actors pose as recruiters from crypto and AI companies

BeatBanker and BTMOB trojans: infection techniques and how to stay safe | Kaspersky official blog
How to protect yourself from the BeatBanker Android trojan, which steals cryptocurrency, hijacks your hardware for crypto mining, and swipes
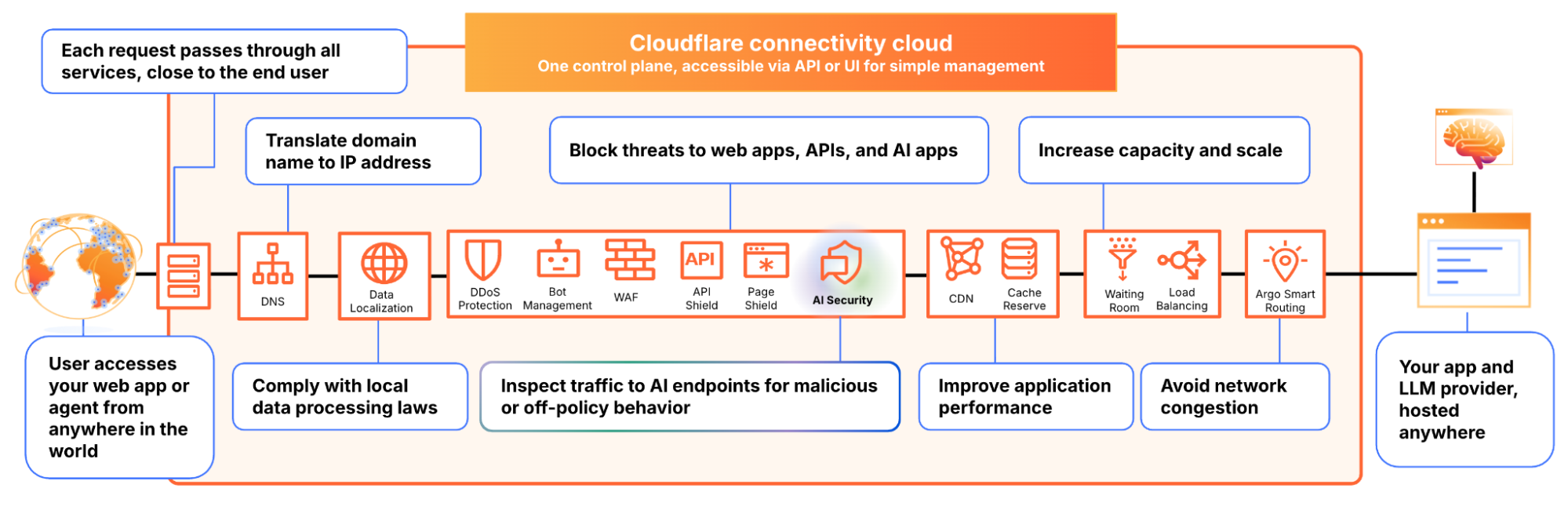
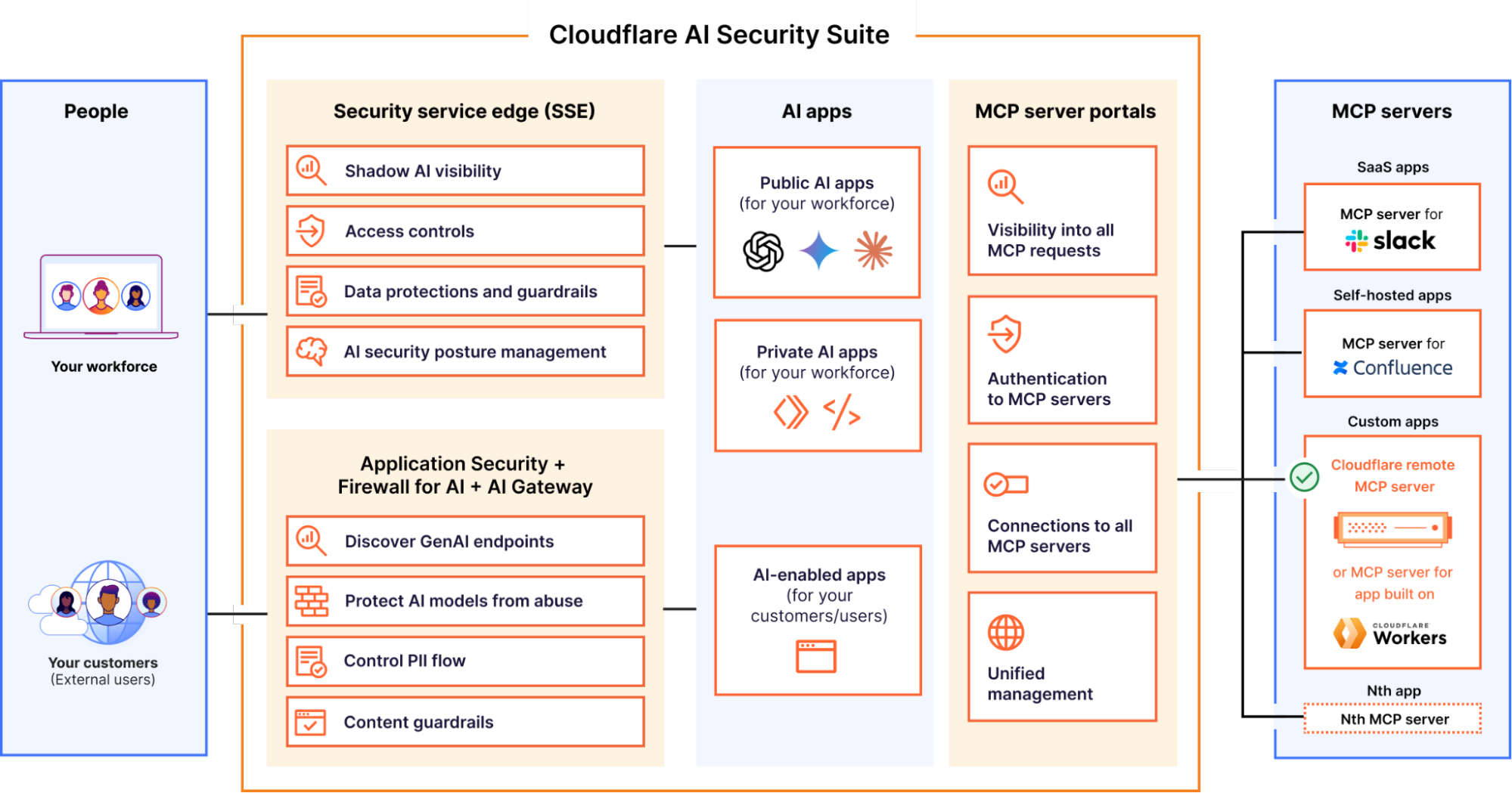
AI Security for Apps is now generally available
Cloudflare AI Security for Apps is now generally available, providing a security layer to discover and protect AI-powered applications, regardless

Slashing agent token costs by 98% with RFC 9457-compliant error responses
Cloudflare now returns RFC 9457-compliant structured Markdown and JSON error payloads to AI agents, replacing heavyweight HTML pages with machine-readable

Iran conflict drives heightened espionage activity against Middle East targets
Analyst note: Proofpoint uses the UNK_ designator to define clusters of activity that are still developing and have not been observed

ANY.RUN & Tines: Scale SOC and Meet SLAs with Intelligent Workflows
In busy SOC environments, every minute spent waiting for threat validation slows containment and impacts response metrics. The ANY.RUN integration with Tines

Through the Lens of MDR: Analysis of KongTuke’s ClickFix Abuse of Compromised WordPress Sites
Our analysis of an active KongTuke campaign deploying modeloRAT — malware capable of reconnaissance, command execution, and persistent access —
Mental health apps are leaking your private thoughts. How do you protect yourself? | Kaspersky official blog
A new study has uncovered hundreds of vulnerabilities in popular mental health apps, including leaks of diagnoses, therapy notes, and
Iranian MOIS Actors & the Cyber Crime Connection
Key Points Iran-linked actors are increasingly engaging with the cyber crime ecosystem. Their activity suggests a growing reliance on criminal
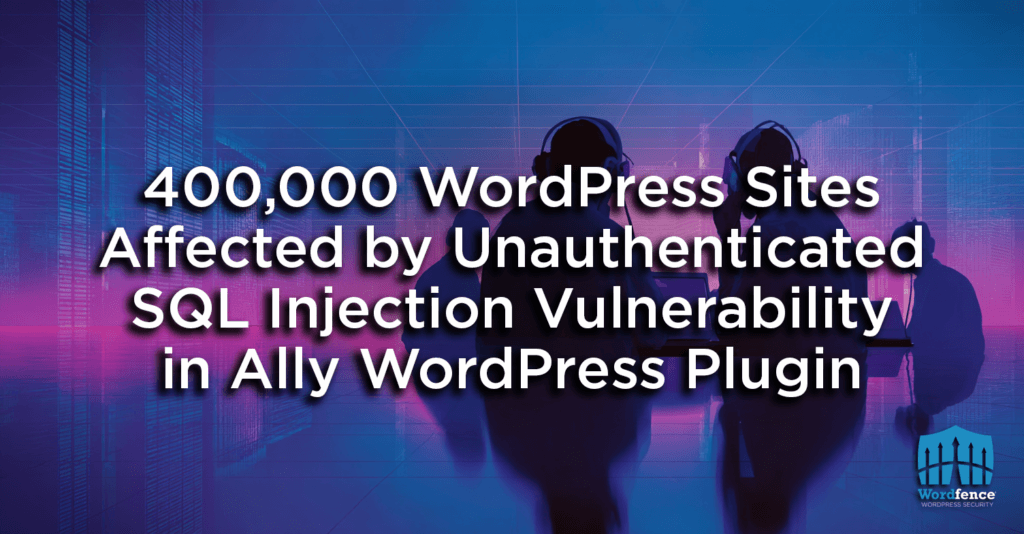
400,000 WordPress Sites Affected by Unauthenticated SQL Injection Vulnerability in Ally WordPress Plugin
On February 4th, 2026, we received a submission for an SQL Injection vulnerability in Ally, a WordPress plugin estimated to

RootViz: New Root DNS Reachability Dashboard
In this guest post, the team at SIDN Labs introduce a new dashboard built on RIPE Atlas data that lets

Building a security overview dashboard for actionable insights
Cloudflare’s new Security Overview dashboard transforms overwhelming security data into prioritized, actionable insights, empowering defenders with contextual intelligence on vulnerabilities.The
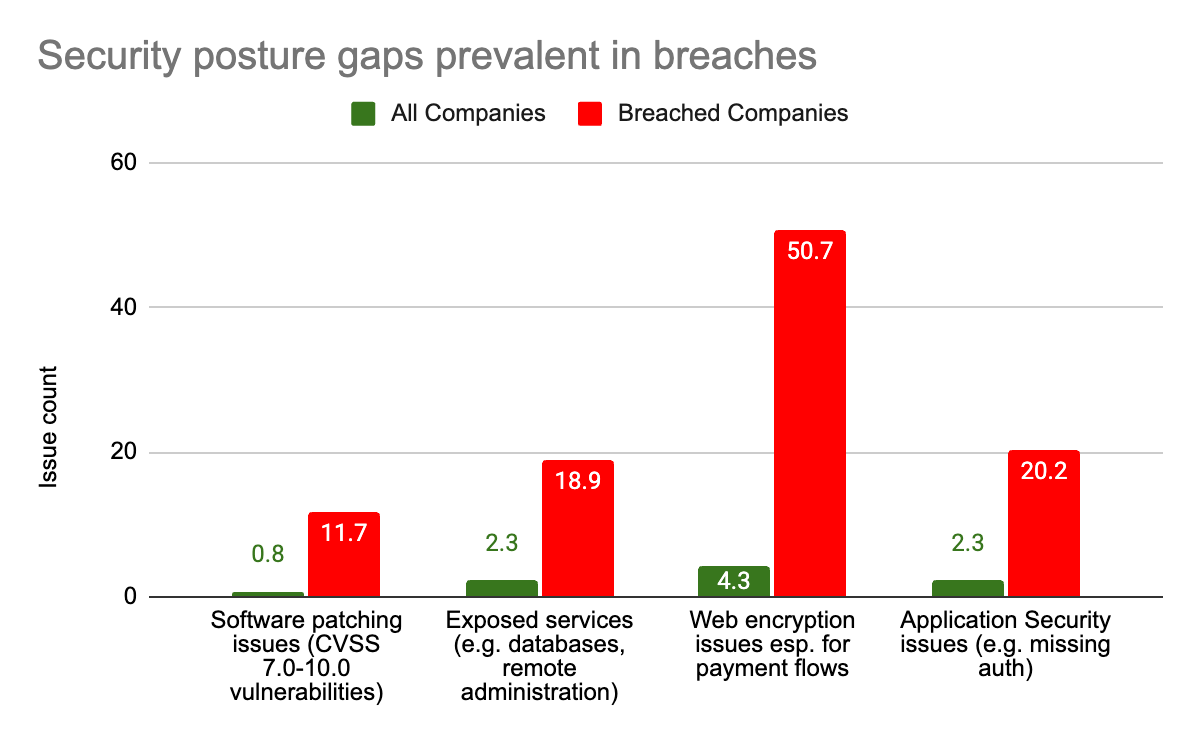
Translating risk insights into actionable protection: leveling up security posture with Cloudflare and Mastercard
Cloudflare will be integrating Mastercard’s RiskRecon attack surface intelligence capabilities to help you eliminate Internet-facing blind spots while continuously monitoring

Investigating multi-vector attacks in Log Explorer
Log Explorer customers can now identify and investigate multi-vector attacks. Log Explorer supports 14 additional Cloudflare datasets, enabling users to

The RSAC 2026 Conference talks worth catching
Threat modeling for AI supply chain risks, disrupting infostealers, and dumb ways to die: We combed through 600+ RSAC 2026
FortiGate Edge Intrusions | Stolen Service Accounts Lead to Rogue Workstations and Deep AD Compromise
FortiGate SSO flaws allows attackers to steal configs, abuse AD creds, deploy RMM tools, and exfiltrate NTDS files.SentinelOneRead More

The RIPE Chair Team Reports – March 2026
The RIPE Chair Team reports on preparations for RIPE 92, including programme planning and opportunities for community participation, as well

OAuth Device Code Phishing: A New Microsoft 365 Account Breach Vector
ANY.RUN’s analysts are observing a sharp increase in phishing activity abusing Microsoft’s OAuth Device Code flow, with more than 180 phishing URLs

Auditing the Gatekeepers: Fuzzing “AI Judges” to Bypass Security Controls
Unit 42 research reveals AI judges are vulnerable to stealthy prompt injection. Benign formatting symbols can bypass security controls. The

BeatBanker: A dual‑mode Android Trojan
Kaspersky researchers identified a new Android Trojan dubbed BeatBanker targeting Brazil, posing as government apps and Google Play Store, and

Major Cyber Attacks in February 2026: BQTLock, Thread-Hijack Phishing, and MFA Bypass Evolution
February 2026 brought a surge of sophisticated cyber threats targeting businesses across industries. ANY.RUN’s analysts exposed and explored several major

Threat Coverage Digest: New Malware Reports and 2,400+ Detection Rules
February brought another round of major detection improvements across ANY.RUN’s threat intelligence and sandbox coverage. Alongside new Threat Intelligence reports, our analysts expanded behavioral visibility

CISOs in a Pinch: A Security Analysis of OpenClaw
Learn about OpenClaw (a sovereign agent) and how this can be viable for enterprises.Trend Micro Research, News and PerspectivesRead More

9th March – Threat Intelligence Report
For the latest discoveries in cyber research for the week of 9th March, please download our Threat Intelligence Bulletin. TOP
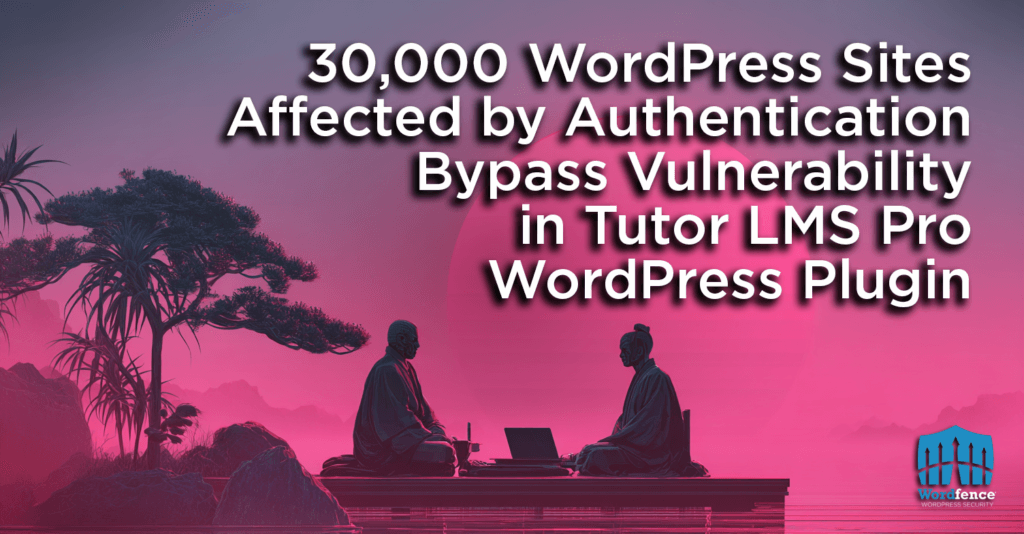
30,000 WordPress Sites Affected by Authentication Bypass Vulnerability in Tutor LMS Pro WordPress Plugin
On December 30th, 2025, we received a submission for an Authentication Bypass vulnerability in Tutor LMS Pro, a WordPress plugin
Complexity is a choice. SASE migrations shouldn’t take years.
Discover how Cloudflare partners TachTech and Adapture are shattering the 18-month migration myth, deploying agile SASE for global enterprises in

Active defense: introducing a stateful vulnerability scanner for APIs
Cloudflare’s new Web and API Vulnerability Scanner helps teams proactively find logic flaws. By using AI to build API call

Secure agentic AI for your Frontier Transformation
Learn how Microsoft Agent 365 and Microsoft 365 E7 can help secure your Frontier Transformation. The post Secure agentic AI
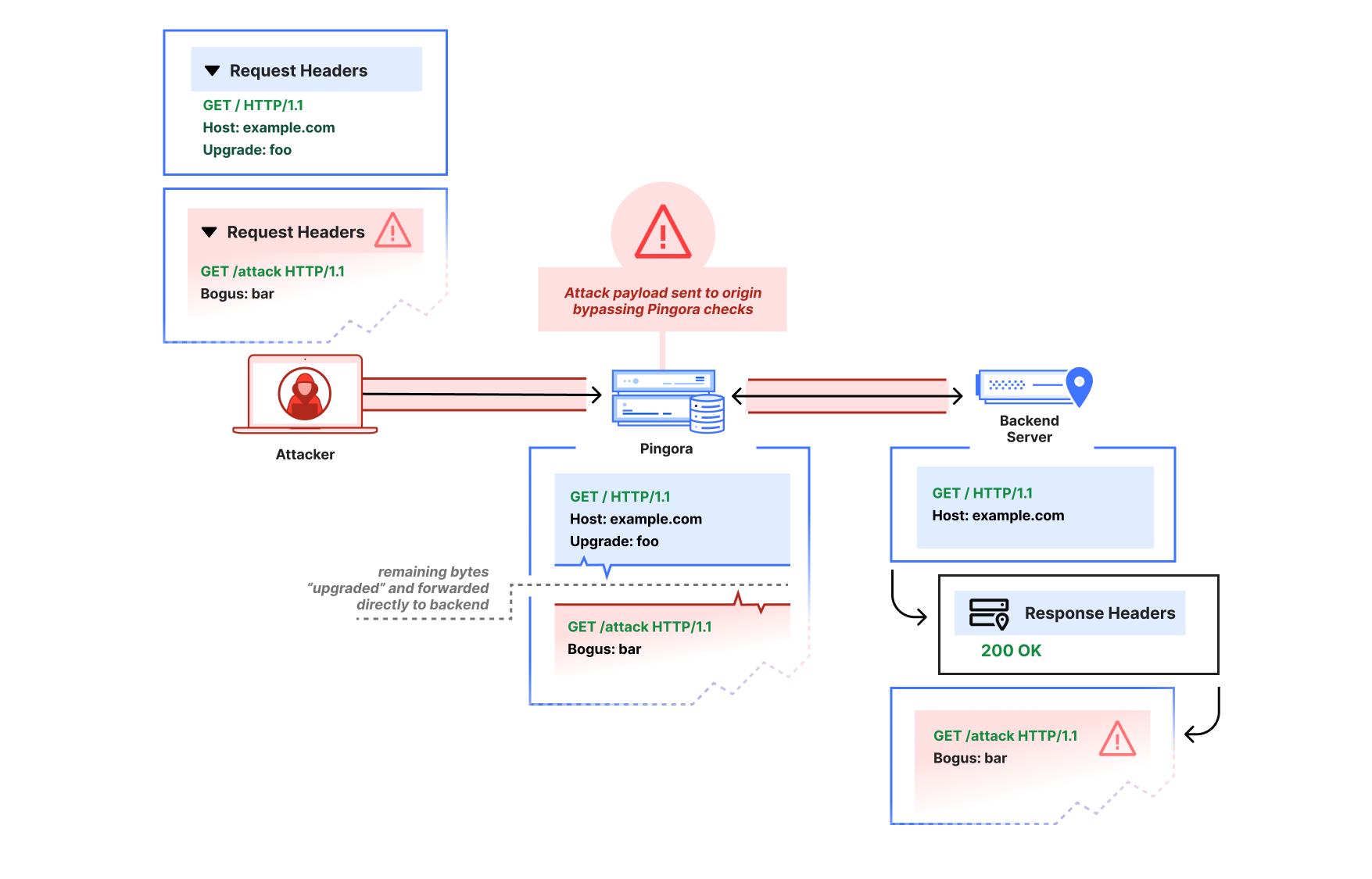
Fixing request smuggling vulnerabilities in Pingora OSS deployments
Today we’re disclosing request smuggling vulnerabilities when our open source Pingora service is deployed as an ingress proxy and how

TrendAI™ at [un]prompted 2026: From KYC Exploits to Agentic Defense
At [un]prompted 2026, TrendAI™ demonstrated how documents can be used to exploit AI-driven KYC pipelines and introduced FENRIR, an automated

Cisco to Power TPG Telecom’s Next Generation Security and Service Operations Across Australia with Splunk
Splunk will help TPG Telecom accelerate its transition to an AIOps-driven Service Operations Centre — boosting service reliability, strengthening security,

IWD2026: Documentary Raises Visibility of Women in Security
If you want to bring something into the light, a cinema projector is an effective tool. Too often, the work

Supporting women — and wellness — in cybersecurity
When Jothi Dugar isn’t battling cybercriminals, she’s helping people be their best, most authentic selves in the workplace.More RSS Feeds:

How the National Cyber Strategy Secures Our Digital Way of Life
Palo Alto Networks applauds the new National Cyber Strategy. We detail our support for key aspects of its six pillars,

From the endpoint to the prompt: a unified data security vision in Cloudflare One
Cloudflare One unifies data security from endpoint to prompt: RDP clipboard controls, operation-mapped logs, on-device DLP, and Microsoft 365 Copilot

The Good, the Bad and the Ugly in Cybersecurity – Week 10
Authorities seize Tycoon2FA & LeakBase, researchers expose Coruna iOS exploits, and hacktivists launch DDoS attacks after U.S.-Israel strikes.SentinelOneRead More
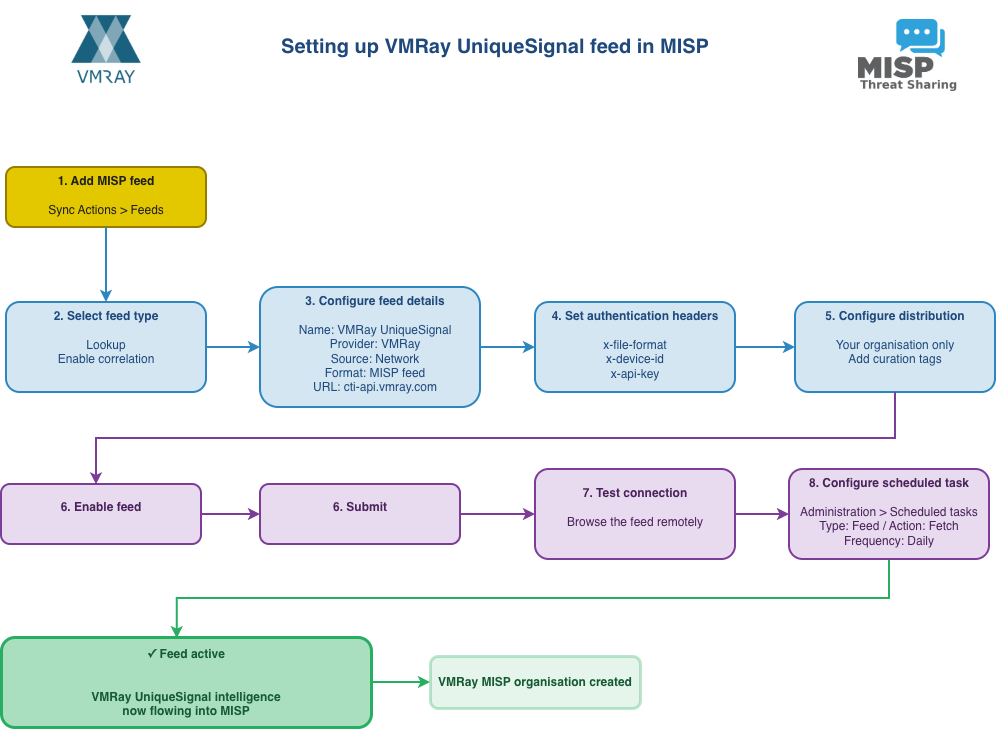
Setting up UniqueSignal in MISP
VMRay UniqueSignal Last year VMRay announced UniqueSignal, a threat intelligence feed that includes: Indicators of Compromise (IOCs) such as IPs, URLs and
An Investigation Into Years of Undetected Operations Targeting High-Value Sectors
In-depth analysis of threat activity we call CL-UNK-1068. We discuss their toolset, including tunneling, reconnaissance and credential theft. The post
Exploits and vulnerabilities in Q4 2025
This report provides statistical data on published vulnerabilities and exploits we researched during Q4 2025. It also includes summary data
Wordfence Intelligence Weekly WordPress Vulnerability Report (February 23, 2026 to March 1, 2026)
Last week, there were disclosed in and that have been added to the Wordfence Intelligence Vulnerability Database, and there were

Women’s History Month: Encouraging women in cybersecurity at every career stage
This Women’s History Month, we explore ways to support the next generation of female defenders at every career stage. The
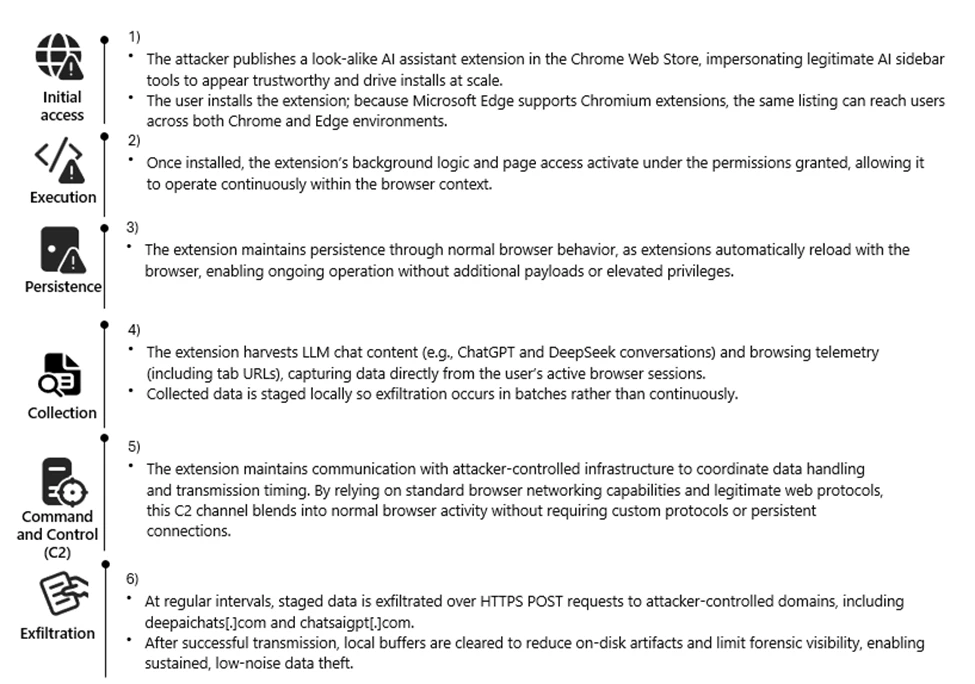
Malicious AI Assistant Extensions Harvest LLM Chat Histories
Malicious AI browser extensions collected LLM chat histories and browsing data from platforms such as ChatGPT and DeepSeek. With nearly

A QUICker SASE client: re-building Proxy Mode
By transitioning the Cloudflare One Client to use QUIC streams for Proxy Mode, we eliminated the overhead of user-space TCP
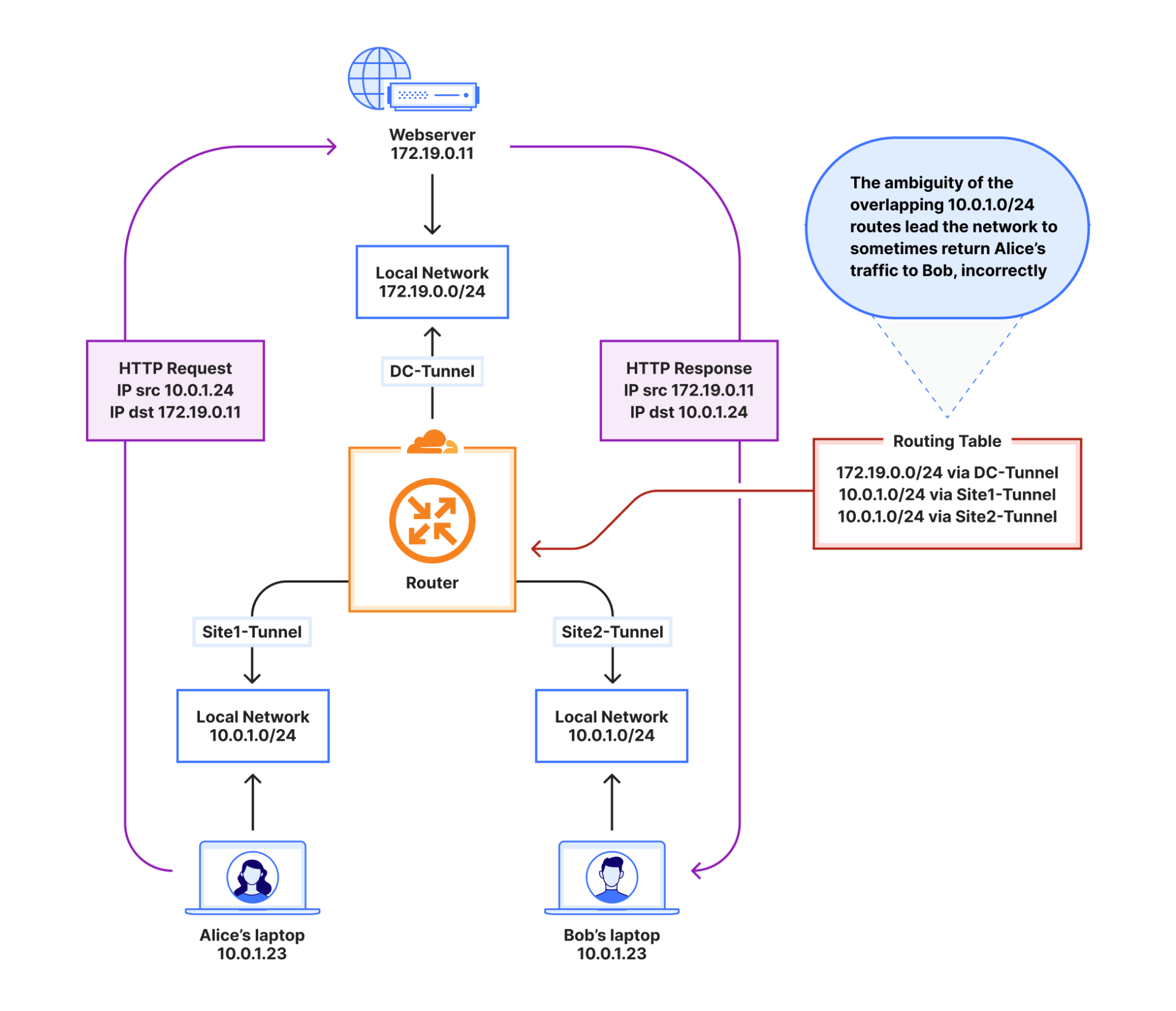
How Automatic Return Routing solves IP overlap
Automatic Return Routing (ARR) solves the common enterprise challenge of overlapping private IP addresses by using stateful flow tracking instead

New BoryptGrab Stealer Targets Windows Users via Deceptive GitHub Pages
The BoryptGrab campaign uses fake SEO‑optimized GitHub repositories and deceptive download pages to distribute a data‑stealing malware family that delivers

Ending the “silent drop”: how Dynamic Path MTU Discovery makes the Cloudflare One Client more resilient
The Cloudflare One Client now features the ability to actively probe and adjust packet sizes. This update eliminates the problems

How Harmonic Proved High-Performance AI Inference on Akamai GPUs
Find out how Harmonic achieved high-performance AI inference on Akamai Cloud with NVIDIA Blackwell GPUs, optimizing for speed and efficiency.BlogRead

Hunting for malicious OpenClaw AI in the modern enterprise
We deconstruct a threat hunt for malicious OpenClaw AI agents, outlining how we identify and migitate risks posed by unauthorized

Rethinking RIPE NCC Navigation
We’ve been looking at how members navigate between RIPE NCC services and where friction appears. This article shares the research

How to avoid the fake buyers flooding Facebook Marketplace
You just sold a stack of old books for $100 on Facebook Marketplace. The buyer seemed eager, messaged instantly, and

How to disable unwanted AI assistants and features on your PC and smartphone | Kaspersky official blog
Detailed instructions for disabling intrusive AI features in popular services and operating systems.Kaspersky official blogRead More

Europol, Microsoft, TrendAI™ and Collaborators Halt Tycoon 2FA Operations
Tycoon 2FA was dismantled this week by law enforcement and industry partners including TrendAI™. The phishing-as-a-service platform offered MFA bypass

Inside Tycoon2FA: How a leading AiTM phishing kit operated at scale
Tycoon2FA has become a leading phishing-as-a-service (PhaaS) platforms, enabling campaigns that reach over 500,000 organizations monthly, prompting Microsoft’s Digital Crimes
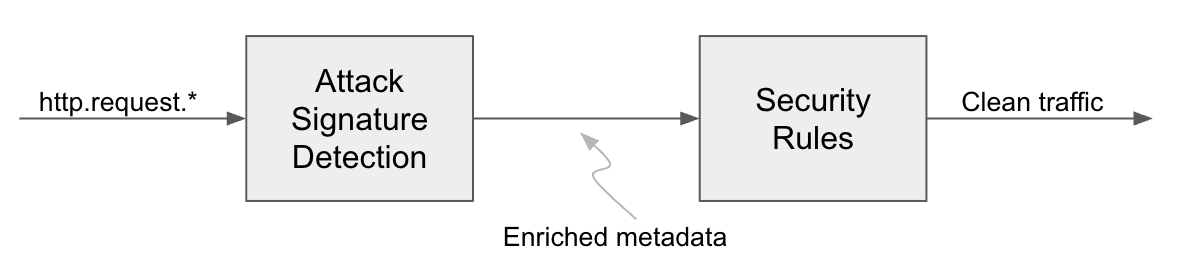
Always-on detections: eliminating the WAF “log versus block” trade-off
Cloudflare is introducing Attack Signature Detection and Full-Transaction Detection to provide continuous, high-fidelity security insights without the manual tuning of

Disruption targets Tycoon 2FA, popular AiTM PhaaS
Key findings Tycoon 2FA is one of the most popular phishing-as-a-service (PhaaS) platforms currently used by threat actors, and highest
Defeating the deepfake: stopping laptop farms and insider threats
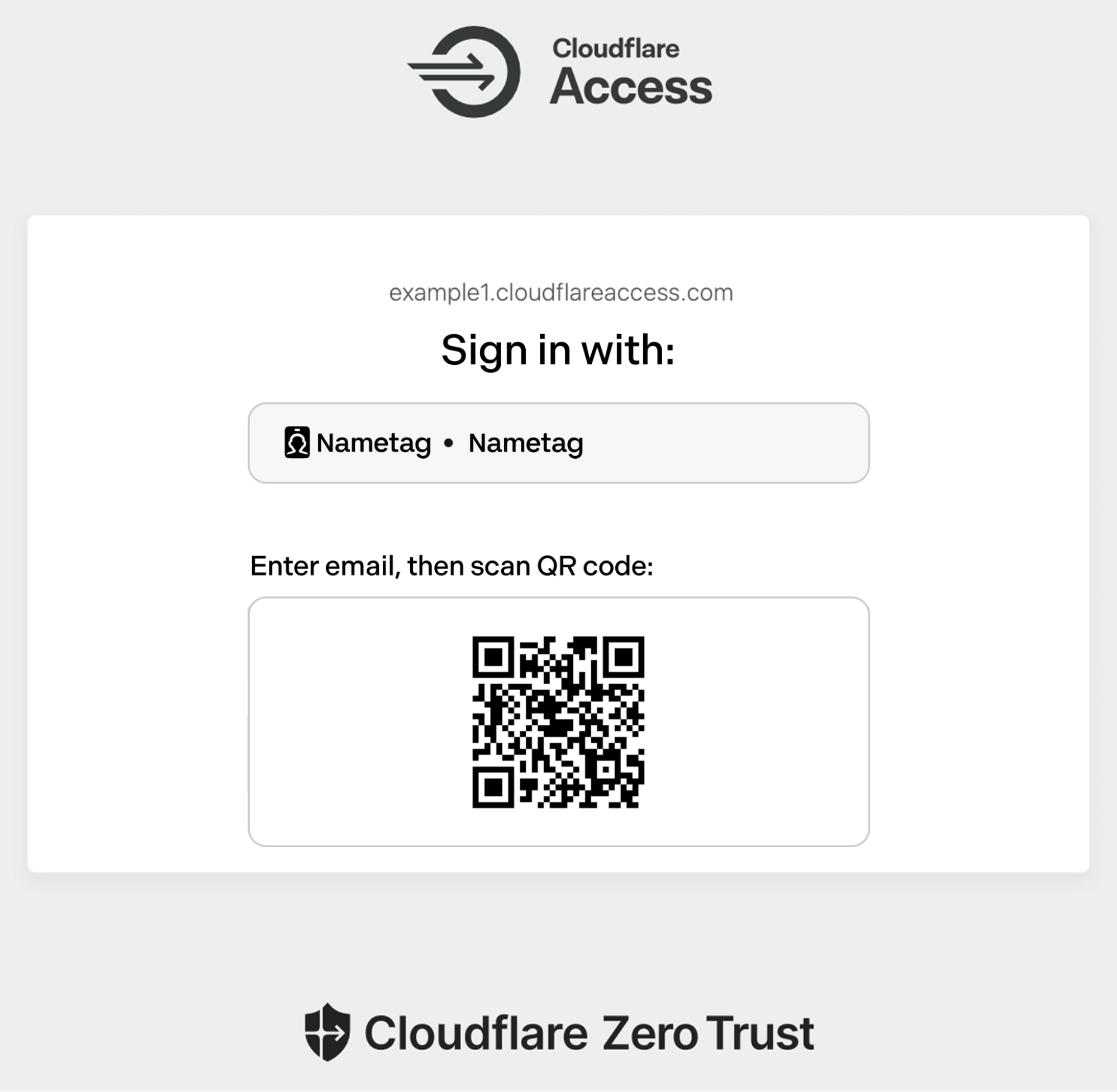
Cloudflare One is partnering with Nametag to combat laptop farms and AI-enhanced identity fraud by requiring identity verification during employee
Stop reacting to breaches and start preventing them with User Risk Scoring
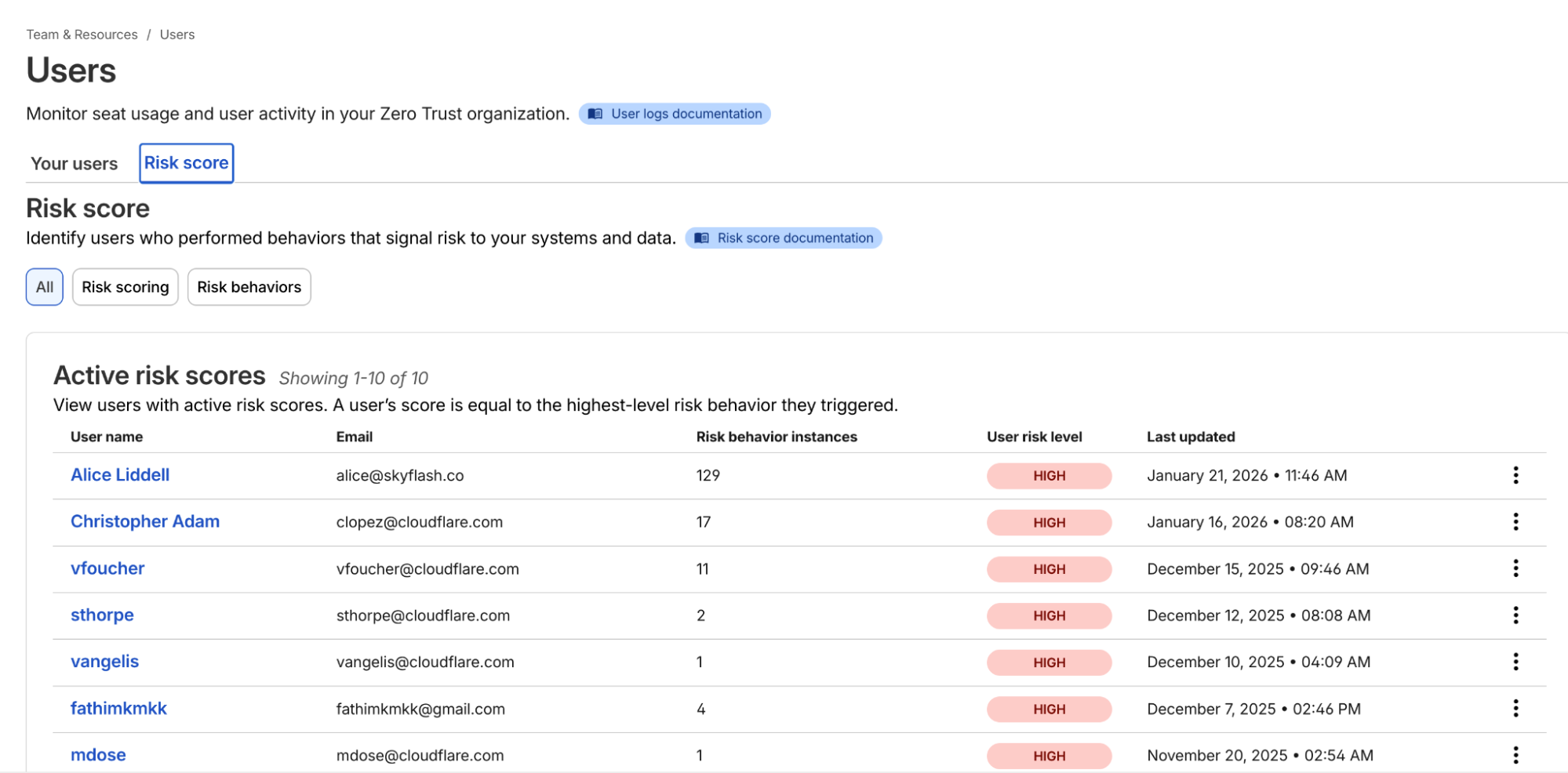
Cloudflare One now incorporates dynamic User Risk Scores into Access policies to enable automated, adaptive security responses. This update allows
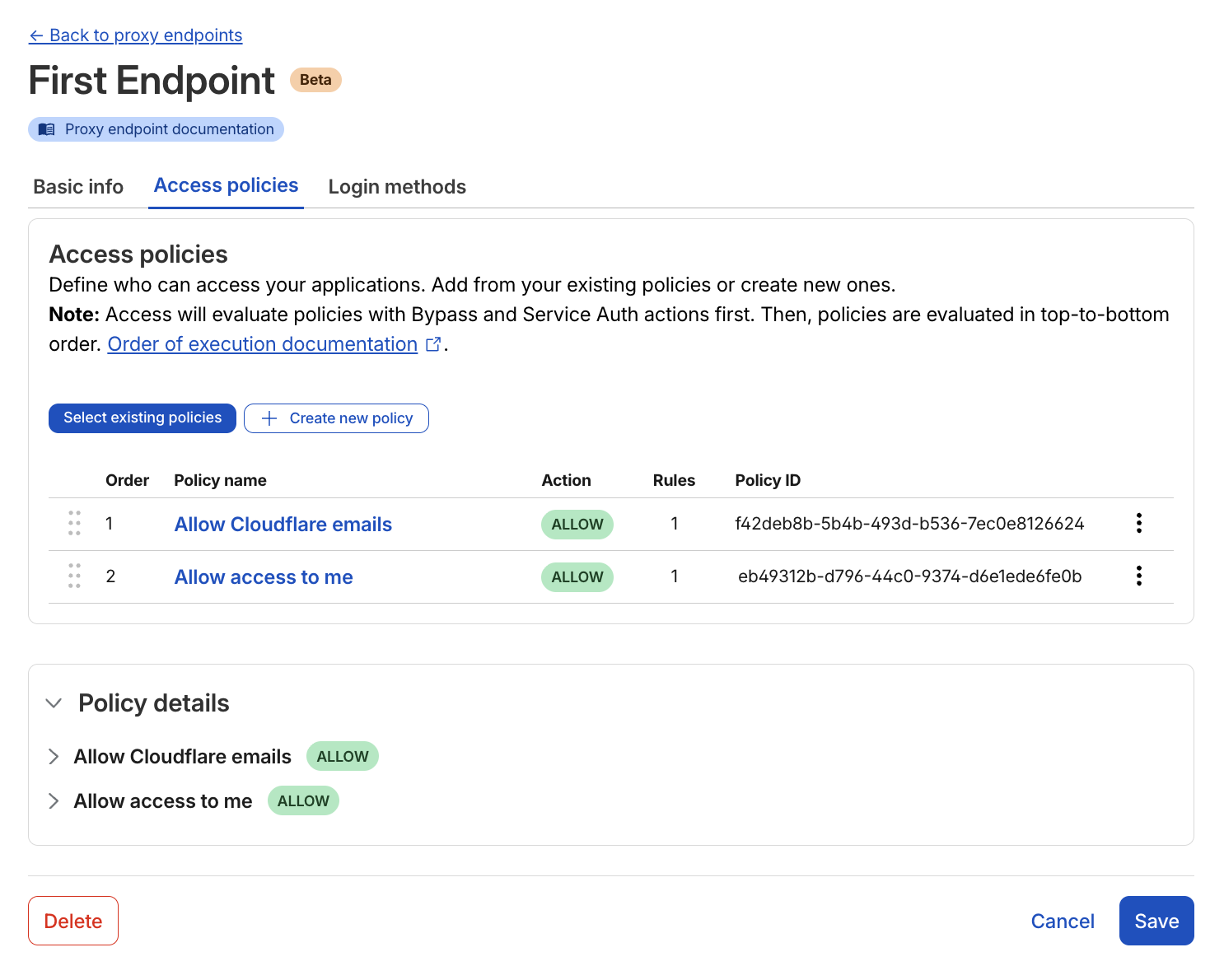
Moving from license plates to badges: the Gateway Authorization Proxy
Cloudflare’s Gateway Authorization Proxy adds support for identity-aware policies for clientless devices, securing virtual desktops, and guest networks without a
Mind the gap: new tools for continuous enforcement from boot to login
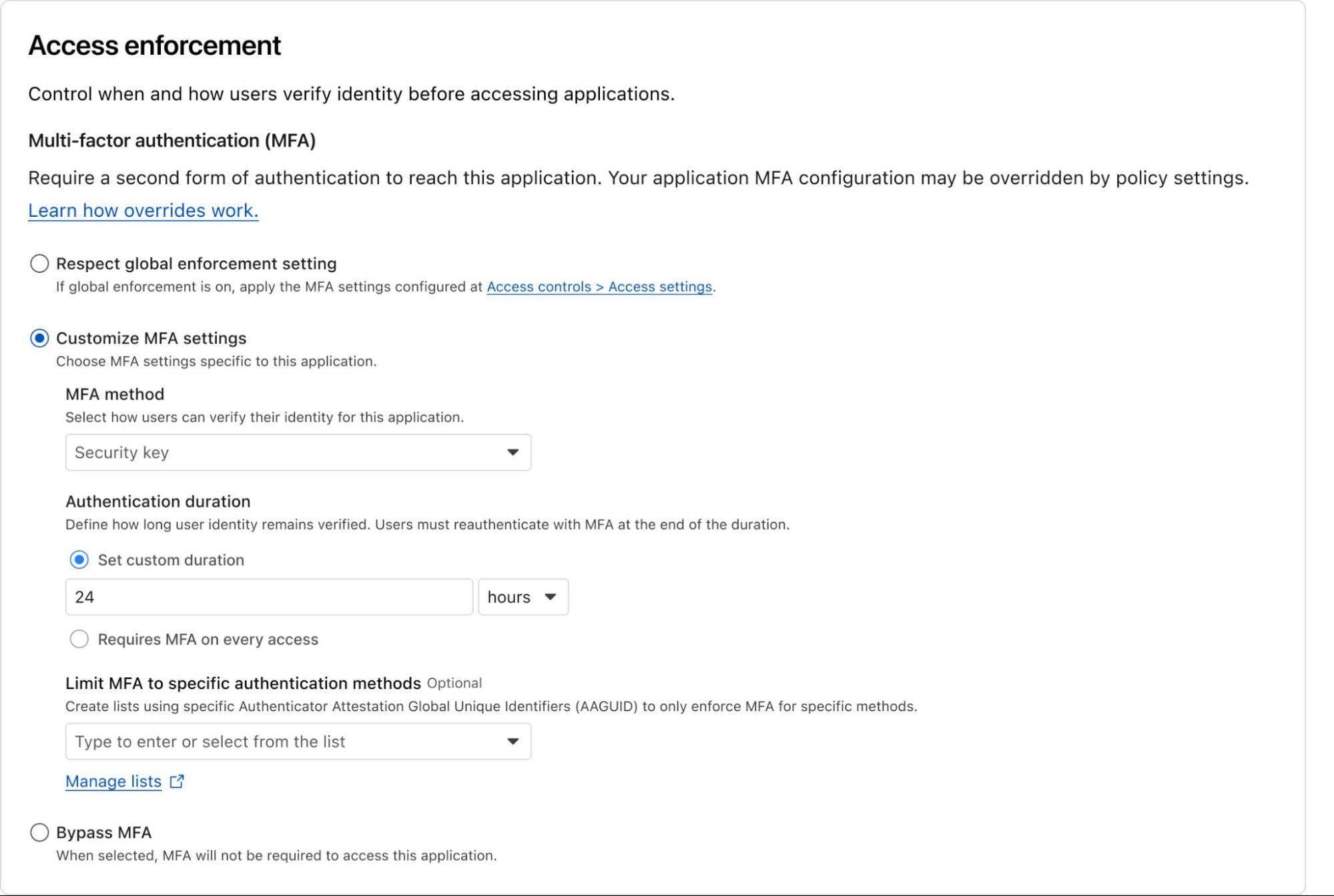
Cloudflare’s mandatory authentication and independent MFA protect organizations by ensuring continuous enforcement, from the moment a machine boots until sensitive

What a browser-in-the-browser attack is, and how to spot a fake login window | Kaspersky official blog
Explaining how the browser-in-the-browser phishing technique works, why fake login windows look just like the real thing, and the red

Breaking down a supply chain attack leveraging a malicious Google Workspace OAuth app
How to detect and respond to OAuth consent attacks in Google WorkspaceRed CanaryRead More

Mobile malware evolution in 2025
Statistics on Android malware and the most notable mobile threats of 2025: preinstalled backdoors Keenadu and Triada, spyware Trojans, the

Interplay between Iranian Targeting of IP Cameras and Physical Warfare in the Middle East
Key Findings Introduction As highlighted in the Cyber Security Report 2026, cyber operations have increasingly become an additional tool in interstate
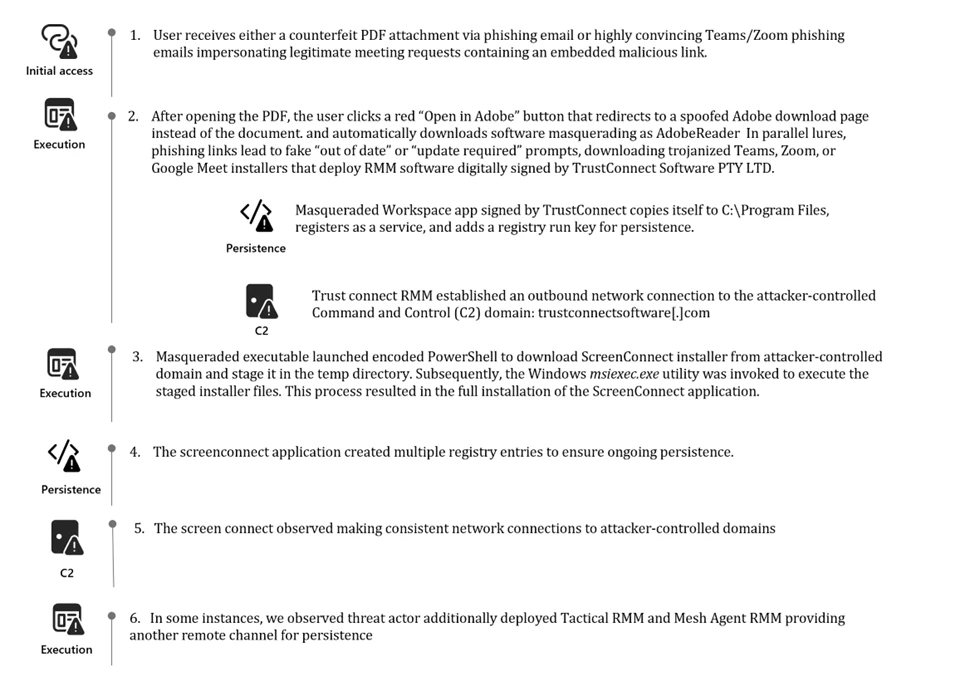
Signed malware impersonating workplace apps deploys RMM backdoors
Signed malware backed by a stolen EV certificate deployed legitimate RMM tools to gain persistent access inside enterprise environments. Organizations

Why GPU Card Counts Matter for Real AI Workloads
Stay ahead with NVIDIA RTX PRO™ 6000 Blackwell Server Edition GPUs in the Akamai Inference Cloud. Discover the right GPU

Silver Dragon Targets Organizations in Southeast Asia and Europe
Silver Dragon Targets Organizations in Southeast Asia and Europe Key Findings Introduction In recent months, Check Point Research (CPR) has
AI assistant in Kaspersky Container Security
The Kaspersky Container Security solution (part of the Kaspersky Cloud Workload Security offering) now has an OpenAI API interface for

From reactive to proactive: closing the phishing gap with LLMs
Email security is a constant arms race. Like WWII engineers reinforcing only the planes that returned, survivorship bias hides real

See risk, fix risk: introducing Remediation in Cloudflare CASB
Cloudflare CASB Remediation lets security teams go beyond visibility to fix risky file sharing in Microsoft 365 and Google Workspace
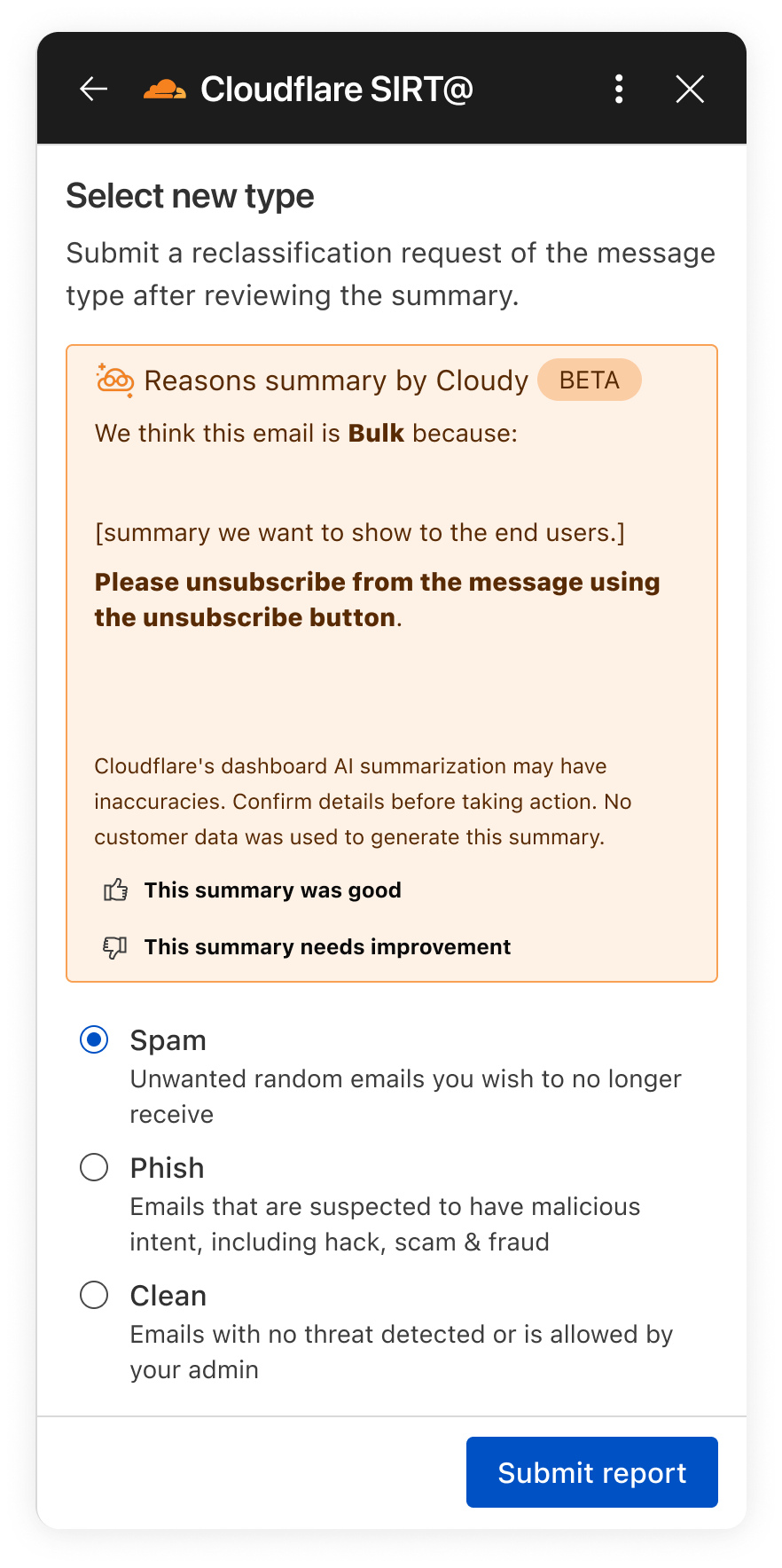
How Cloudy translates complex security into human action
Cloudy is our LLM-powered explanation layer built directly into Cloudflare One. Its explanations, now part of Phishnet and API CASB,

Evolving Cloudflare’s Threat Intelligence Platform: actionable, scalable, and ETL-less
Stop managing ETL pipelines and start threat hunting. Introducing new visualization, automation, and enrichment tools in the Cloudflare Threat Intelligence

Introducing the 2026 Cloudflare Threat Report
There has been a fundamental shift toward industrialized cyber threats, highlighted by a record 31.4 Tbps DDoS attack and sophisticated

Fooling AI Agents: Web-Based Indirect Prompt Injection Observed in the Wild
Uncover real-world indirect prompt injection attacks and learn how adversaries weaponize hidden web content to exploit LLMs for high-impact fraud.

A Day in the Life of RIPE Atlas
On any given day, RIPE Atlas generates billions of measurement results, offering a comprehensive view of connectivity and reachability worldwide.

CISOs in a Pinch: A Security Analysis of OpenClaw
Learn how Claude Code Security set Cybersecurity stocks on fire.Trend Micro Research, News and PerspectivesRead More
